Hello everyone! Here are the release notes for the most recent updates we’ve made to Duo.
You can subscribe to notifications for new release notes by following the process described here. If you have any questions about these changes, please comment below.
Features, enhancements, and other improvements
New Administrative Units feature
- Administrative Units enables Duo Beyond, Duo Access, and Duo MFA customers to group Duo users and applications and grant management privileges to designated administrators. It is intended to be used in tandem with administrator roles.
- A Duo administrator’s assigned role determines which actions that admin may perform.
- A Duo administrator’s assigned administrative unit determines which objects (policies, user groups, and applications) that administrator can manage by performing the actions permitted by the admin’s role.
- Here’s an example of how an administrator’s actions and access can be restricted by their role in an Administrative Unit:

- Only Duo administrators with the Owner role may create administrative units or modify a unit’s assigned administrators, user groups, and applications.
- Learn about how to create, modify, and use Administrative Units in the documentation.
New Administrator Actions log action
Administrators’ viewing of users’ bypass codes is now logged.
New and updated applications
Version 2.9.0 of the Duo Authentication Proxy released
- This new version of the Duo Authentication Proxy for Windows and Linux includes a connectivity tool to troubleshoot general connectivity issues. This tool is not backward-compatible with prior Authentication Proxy releases.
- The tool can be run automatically at startup or on-demand. Learn about how to configure and use this new tool in the documentation.
- Note that this is not a configuration utility. It will not walk you through setting up the Duo proxy services, but can help you figure out issues such as an inability to listen on a port, inability to contact remote servers, inability to communicate with the Duo cloud service, and similar problems.
- Other changes in this version of the Authentication Proxy are as follows:
- Python 2.7 is now bundled with the Authentication Proxy installation.
- The HTTP Proxy feature now accepts CIDR ranges as permitted client_ip values.
- The previously Windows-only EAP/TLS 1.2 fix for NetMotion has been added to Linux.
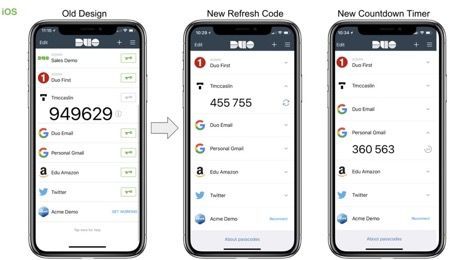
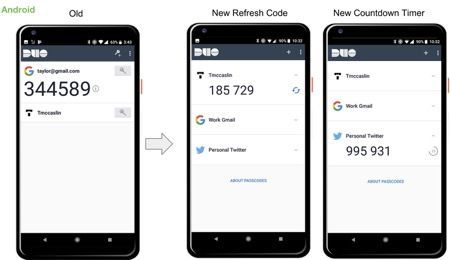
Version 3.21.0 of the Duo Mobile App for iOS and Android released
- This update for iOS and Android includes an improved main account list and other changes. Learn more about these changes in this Community post. Key highlights are as follows:
- We removed the key icon.
- New TOTP countdown timer for third-party accounts.
- New HOTP refresh button for Duo-protected accounts.
- Refined spacing, sizing, and wording.
- Simplified language and help text.
Bug fixes
- The Admin API /admin/v1/users endpoint was not returning U2F tokens in the response. This has been corrected.
- When linking from the Denied Authentications report to the Authentication Log, the time range filter did not persist and “User marked fraud” did not properly filter. Both of these issues have now been fixed.