- Cisco Community
- Technology and Support
- Security
- Duo Security
- Duo Release Notes
- D246: Duo Release Notes for August 5, 2022
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 08-05-2022 07:12 AM
Hello everyone! Here are the release notes for the most recent updates we’ve made to Duo.
You can subscribe to notifications for new release notes by following the process described here. If you have any questions about these changes, please comment below.
What’s in this release?
New features, enhancements, and other improvements
- Duo Single Sign-On Improvements
- Duo Directory Sync Now Supports Reuse of Azure AD Connection
- Improved Bypass Code UI in the Duo Admin Panel
- Deprecated Endpoints in the Duo Admin API
New and updated applications
- Ivanti Connect Secure Now Available for Duo Single Sign-On
- Duo Device Health Application Public Beta for macOS and Windows Version 2.27.2
- Duo Device Health Application for macOS and Windows Version 2.28.0
- Duo Mobile 4.21.1 for Android
- Duo Mobile 4.21.0 for iOS
Bug fixes
New features, enhancements, and other improvements
Duo Single Sign-On improvements
- Duo’s Amazon Web Services application now supports custom session duration limits of 15 minutes to 12 hours, configured in units of seconds.
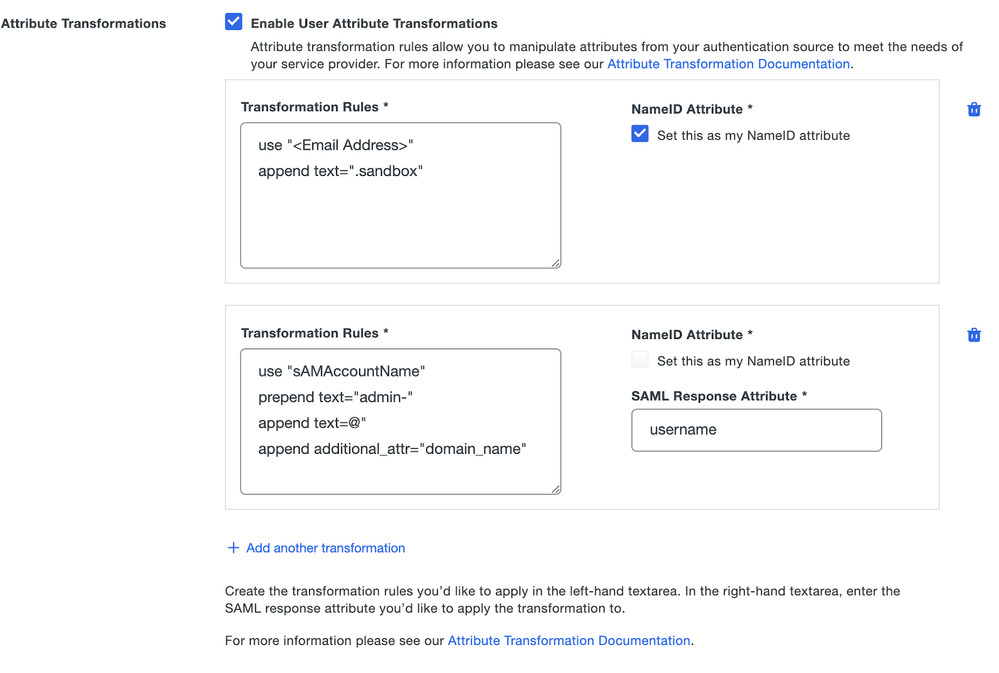
- You can now use Duo Single Sign-On attribute transformations in a generic SAML application to transform identity provider attributes to meet service provider requirements.
- For example, you can transform a NameID attribute by appending text, sending jdoe@example.com.sandbox to the service provider.
Duo Directory Sync now supports reuse of Azure AD connection
- Administrators can now choose to reuse an existing authorized Microsoft Azure AD connection when adding a new Azure Active Directory sync.
Improved bypass code UI in the Duo Admin Panel
- Generating user bypass codes now displays a link to the bypass code table rather than the code itself.
- You can click to hide bypass codes after viewing them, or copy hidden bypass codes without revealing them.
- Duo hides bypass codes automatically after 30 seconds.
Deprecated endpoints in the Duo Admin API
- The helpdesk_message parameter of the Settings endpoint has been deprecated in favor of improved functionality provided by the Custom Messaging endpoint. Settings endpoint functions are impacted as follows:
- Retrieve Settings: The helpdesk_message parameter in the response will no longer be populated. It will always be an empty string.
- Modify Settings: The helpdesk_message parameter, if provided, will be ignored.
- The Logo endpoint has also been deprecated in favor of improved functionality provided by the Custom Branding endpoint, which affects the following functions:
- Retrieve Logo will continue to function as before, but it is deprecated.
- Modify Logo: will continue to function as before, but it is deprecated.
- Delete Logo: will continue to accept calls but will not delete the logo.
New and updated applications
Ivanti Connect Secure now available for Duo Single Sign-On
- Ivanti Connect Secure is now available as a protected application configured to use Duo Single Sign-On as its SAML identity provider.
Duo Device Health application public beta version 2.27.2 released
-
macOS beta version 2.27.2.0
- Minor improvements and enhancements.
-
Windows beta version 2.27.2
- Added an optional parameter to the support script that specifies which user to gather logs from.
- Added ability to control debug log setting via an HKLM registry key.
- Minor improvements and enhancements.
Duo Device Health application production version 2.28.0 released
-
macOS version 2.28.0.0
- Minor improvements and enhancements.
-
Windows version 2.28.0
- Added an optional parameter to the support script that specifies which user to gather logs from.
- Added ability to enable debug logging via registry key.
- Fixed an issue when collecting device identifiers that could cause health reports to fail.
- Minor improvements and enhancements.
Duo Mobile for Android version 4.21.1 released
- Miscellaneous bug fixes and behind-the-scenes improvements.
Duo Mobile for iOS version 4.21.0 released
- Miscellaneous bug fixes and behind-the-scenes improvements.
Bug fixes
- Resolved an Duo Admin Panel error message that resulted from an administrator successfully resending an enrollment code.
- Removed a duplicate warning icon from the Directory Sync Users page in the Admin Panel.
- Fixed a privilege escalation vulnerability that allowed an administrator with the Billing role to become an effective Owner by downgrading to the Duo Free edition if the account had fewer than 10 users. This issue was fixed in D244, which finished releasing July 7, 2022.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
I’m confused. Version 5.7.2 is the newest release and that was on 7/23. Why am I getting another email about release notes when there is no new version? All I want is to be made aware of when there is a new version and the release notes for it. How is Duo making this so frickin complicated???
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi @BetterThanRSA, I’m sorry about the confusion.
It sounds like what you need is information about the latest updates to Duo Authentication Proxy, which last updated to version 5.7.2 on June 23.. That’s just one of our products, and these Community Release Notes are how we publish changes made to all Duo products. When we release Authentication Proxy updates, they’ll be in the Community Release Notes and on the website docs.
You might also want to check out our Authentication Proxy community forum:
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: