- Cisco Community
- Technology and Support
- Security
- Duo Security
- Managing Users
- Azure AD Sync - Account Permissions
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Azure AD Sync - Account Permissions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-10-2017 10:17 AM
I am having an issue with configuring Azure AD Sync.
When I use a Global Administrator Account in Azure, I am able to configure and set up the sync.
When I scale the permissions back in Azure to a Service Administrator, I receive an error that the account can’t access the application.
I really don’t want the sync account to be a global admin in Azure.
Has anyone figured out the least privilege access required for the azure sync to work properly?
- Labels:
-
Directory Sync
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-21-2017 02:36 PM
Hi bendretread,
That’s a great question! Azure AD roles have changed a bit since we first released the Azure Sync feature, so I tested it again.
I created a “limited administrator” Azure AD account, and tried adding on roles to see if the sync would work. Even with all of the available admin roles in the UI granted, that limited admin couldn’t authorize consent for Duo Azure Sync.
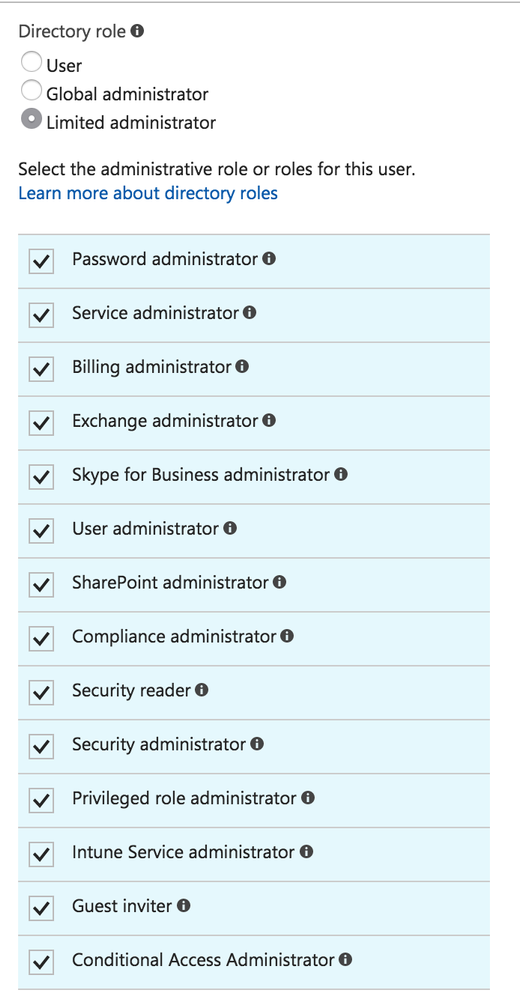
Of course, once I changed the role from Limited to Global admin I could consent as that user.
We’ll do some more research into whether it’s possible to grant the necessary rights for consent outside of the GUI (not immediately though, just to set expectations).
I do want to reassure you that Duo doesn’t store the consent user’s username and password directly. After you authorize the Duo Azure Sync app it uses an OAUTH token to access your tenant. You also aren’t authorizing write access to your AAD tenant by Duo.
You can view the delegated permissions used by the Duo Azure Sync app in the Azure portal under Azure Active Directory > App registrations > Duo Security Azure Sync > Settings > Required permissions > Windows Azure Active Directory.
Thanks for using Duo!
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide