- Cisco Community
- Technology and Support
- Security
- Duo Security
- Deployment Strategy
- Why is not recommend installing the DAP on the same Windows AD?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-08-2023 04:50 AM
Hi All,
I found a very interesting and wonder article in “Duo Authentication Proxy - Reference”.
We do not recommend installing the Duo Authentication Proxy on the same Windows server that acts as your Active Directory domain controller or one with the Network Policy Server (NPS) role. If you must co-locate the Duo Authentication Proxy with these services, be prepared to resolve potential LDAP or RADIUS port conflicts between the Duo service and your pre-existing services.
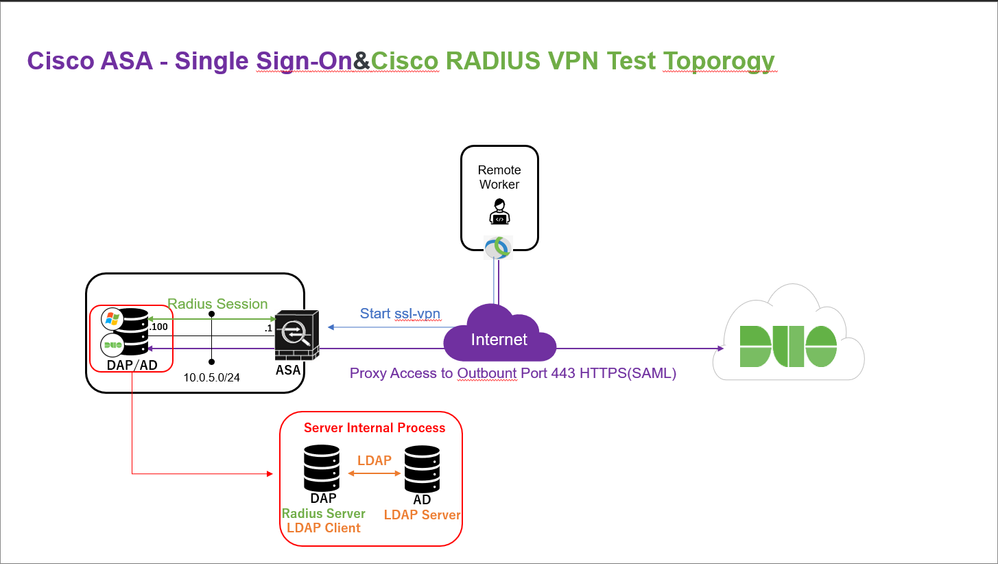
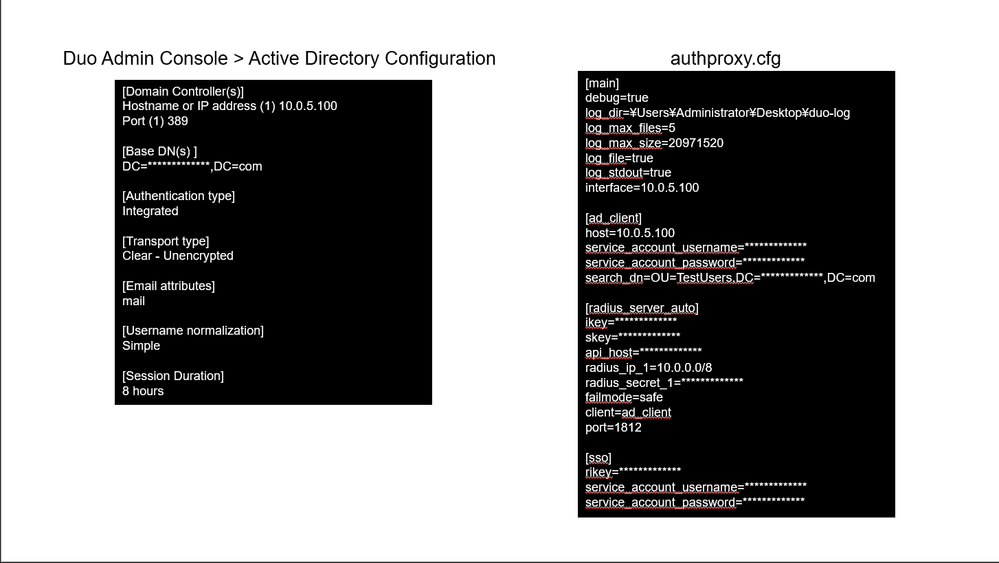
In my opinion, there should be no port conflict if AD and DAP are built on the same Windows server. In fact, I tried that with the attached my configuration and setup image and it worked exactly as I expected it to.
Does anyone know why it is not recommended? Has anyone done a similar test and encountered any problems?
Regards,
Raima Ito
Solved! Go to Solution.
- Labels:
-
Deployment Strategy - General
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-11-2023 11:03 PM
Hi Raima,
I can help clear up why we recommend the above.
There are a few of reasons for this recommendation.
In general it is best practice to keep your DC as clean as possible as it is a critical piece of your domain architecture.
Having a distinct proxy and DC server, or more to the point multiple of each will allow for high availability and avoids a single point of failure, whilst also assisting with troubleshooting in the event of an issue with one of the systems and faster recovery.
Finally and as per the documentation:
If you must co-locate the Duo Authentication Proxy with these services, be prepared to resolve potential LDAP or RADIUS port conflicts between the Duo service and your pre-existing services.
The proxy can act both as a RADIUS, and an LDAP server. Your DC is an LDAP server, and as such if you install your proxy on your DC, they will both try use ports 389/636 which is a port conflict.
The same applies with RADIUS, such as installing the proxy on an NPS server or even making your DC an NPS server as well as a Duo Authentication Proxy would mean a port conflict with port 1812.
Both of the above are avoidable if you define custom ports for the proxy for LDAP or RADIUS if you have any conflicts.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-11-2023 11:03 PM
Hi Raima,
I can help clear up why we recommend the above.
There are a few of reasons for this recommendation.
In general it is best practice to keep your DC as clean as possible as it is a critical piece of your domain architecture.
Having a distinct proxy and DC server, or more to the point multiple of each will allow for high availability and avoids a single point of failure, whilst also assisting with troubleshooting in the event of an issue with one of the systems and faster recovery.
Finally and as per the documentation:
If you must co-locate the Duo Authentication Proxy with these services, be prepared to resolve potential LDAP or RADIUS port conflicts between the Duo service and your pre-existing services.
The proxy can act both as a RADIUS, and an LDAP server. Your DC is an LDAP server, and as such if you install your proxy on your DC, they will both try use ports 389/636 which is a port conflict.
The same applies with RADIUS, such as installing the proxy on an NPS server or even making your DC an NPS server as well as a Duo Authentication Proxy would mean a port conflict with port 1812.
Both of the above are avoidable if you define custom ports for the proxy for LDAP or RADIUS if you have any conflicts.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-12-2023 05:08 PM
Hi Raphka,
Thanks for the answer. This post was treated as spam, so I asked the same question in another thread. I am sorry for same question in another thread
I will use your answer to build a DAP.
Regards,
Raima
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-17-2023 12:30 AM
DAP, or Dynamic Access Policy, is a network policy control tool used to regulate and manage access to a network. It is not recommended to install DAP on the same Windows Active Directory (AD) because it can lead to a number of issues. When DAP is installed on an AD server, it can cause conflicts with the existing AD policies and configuration settings. Additionally, DAP is not designed to be installed on the same machine as the AD, so it can cause performance issues or even crashes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-17-2023 07:29 AM
Thanks for the response @jospehmack but in this thread “DAP” is being used as shorthand for the Duo Authentication Proxy, which is an application installed to add MFA to on-premises LDAP or RADIUS applications, or to facilitate LDAP or AD directory sync to Duo.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-28-2023 02:08 AM
Installing the DAP on the same Windows AD is not recommended due to potential security risks. The DAP can be used as a way for malicious actors to gain access to sensitive information stored in an organization’s network, which could lead to data breaches and other serious issues. Additionally, installing the DAP on the same Windows AD could cause conflicts with existing applications or services running on that system, leading to instability and performance degradation. It is best practice to install any third-party software such as the DAP onto its own dedicated server instead of sharing resources with existing systems.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: