- Cisco Community
- Technology and Support
- Security
- Duo Security
- Protecting Applications
- Whitelist the Slack application
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Whitelist the Slack application
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-10-2017 12:23 PM
We have a tight global policy where we block browsers that are more than two weeks out of date. We also use OneLogin as our SAML provider and have it configured to use Duo for 2FA.
The Slack application for both Mac and Windows uses an embedded version of Chrome. When our users open Slack, they log in using their OneLogin account. They are then taken to the Duo approval part and are blocked because the version of Chrome used in Slack is more than four months out of date.
Contacting the Slack support team, they responded with:
Unfortunately, while Slack does its best to keep up with Chrome, we’re usually a release or two behind. You’ll need to either whitelist Duo or disable / warn-only browser checks. We consider this an acceptable trade-off because Slack is not a general purpose browser (i.e. it’s not navigating to my-cool-news.ru, only Slack.com). We can mitigate security issues with our app on the server side by detecting and censoring malicious content (i.e. content attempting to exploit the desktop app) far faster than we can by shipping new releases of the Desktop app, unlike the General Purpose Web.
Slack is guaranteed to have the User Agent string “Slack/”, if you want to set up Duo’s whitelist to ignore this entirely. The right-hand side is also guaranteed to be a semver-compatible string if you want to require people to run the latest version of the Slack Desktop app in order to connect.
So what are my options here?
- Labels:
-
Cloud
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-10-2017 01:01 PM
This is a great question. Thanks for raising it! Our recommendation would be to use the Slack web client or Duo Access Gateway rather than your current configuration.
If you were to use the Duo Access Gateway rather than OneLogin + Duo, you’d be able to specify policies at an application level rather than having one standing policy.
Our documentation for protecting Slack via DAG can be found here: https://duo.com/docs/slack.
Here’s more information on creating an application-specific policy: https://duo.com/docs/policy#create-and-apply-a-custom-application-policy.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-12-2017 02:10 PM
To expand on @Dooley 's response-
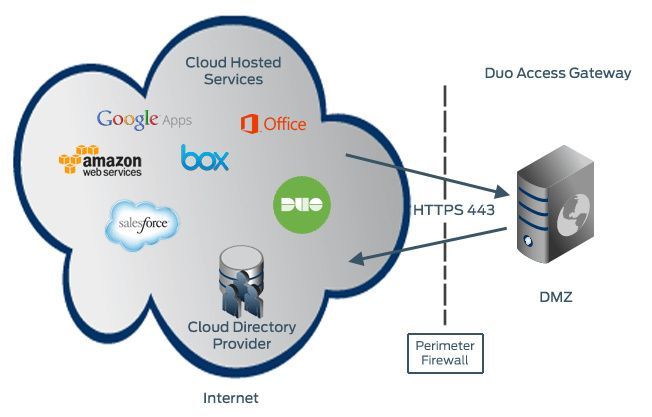
You can use The Duo Access Gateway in addition to OneLogin like so:
This will enable you to take advantage of the Duo Access Gateway Launcher Page as well as separate per app policies. (like not blocking Slack specifically, even though it appears as “out of date”). In this setup, you cloud apps will be federated to the DAG, rather than to OL directly. (OL will still be your SAML IDP).
Cheers
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: