- Cisco Community
- Technology and Support
- Security
- Duo Security
- Managing Users
- Unix Duo for Linux Ubuntu
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-04-2021 01:57 PM
Hello,
I am new to setting up Duo 2FA for Unix, yet new to Linux environment also. I have followed both log_duo and pam_duo instructions. What I am trying to figure out is how to implement Unix 2FA with an existing Duo User. I realized that when I “tested” pam_duo/login_duo, it generates creates a “root” user in the Duo Admin Panel. That is what I did not want. I would like Unix Duo to be carried thru an existing Duo User. Is there a way to divert this to an existing Duo User, such that it does not utilize a license?
Also is there a way to prevent from going to root@“username” after authenticating in Linux?
Solved! Go to Solution.
- Labels:
-
Groups
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-21-2021 12:04 PM
Yes, devices are attached to users only, not users AND endpoints, so a Duo user can authenticate to any application for which they are permitted using the same device, as long as the device type is permitted for those applications.
User A has an account on Computer A & B. Can User A authenticate his account on Computer A & B using one device ?
Yes, if User A exists in Duo with Phone A, and User A is permitted to log into the Duo applications installed on Computer A and B, User A can log into Computer B and authenticate with Phone A.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-10-2021 10:40 AM
Hi @skylin3r92 ,
Sorry to hear you’re having issues with your Duo Unix install.
I have followed both log_duo and pam_duo instructions.
Typically customers install either pam_duo or login_duo. Is there a reason why you would want to install both? If not, I suggest you remove login_duo and just use PAM.
I realized that when I “tested” pam_duo/login_duo, it generates creates a “root” user in the Duo Admin Panel
Did you test it as root? That could explain why it wanted you to enroll a root user in Duo. Configured correctly, it should only need the actual user logging in enrolled as a Duo user.
Also is there a way to prevent from going to root@“username” after authenticating in Linux?
I’m not sure what this means?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-26-2021 10:38 AM
Hi Kristina,
Thank you for your response. I figured out how to do away with the root issue.
I have performed pam_duo. However, once I logged off and tried to log back in, it appears I have been locked out regardless if my password is correct. I see on the documentation for Pam_Duo “We recommend leaving a root shell open while making any changes to your PAM or sshd configuration, in order to prevent accidentally locking yourself out. Additionally, always make sure your PAM configuration works locally before testing it with SSH logins.”
Can you give me details of how to approach this? I have little knowledge about how SSH works.
Also, is it possible to implement the authentication push after to logging in? Such as: Entering username, password, then authenticate. If so, can you point where in the config file I will need to make changes?
I know I’m going off topic here but if I need to create a new topic, please let me know.
Thanks!
-skylin3r92
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-26-2021 02:27 PM
Does your PAM configuration match the examples for your version of Ubuntu shown here: Duo Unix - 2FA for SSH with PAM Support (pam_duo) | Duo Security?
Also, if you scroll down that same doc page to Duo Unix - 2FA for SSH with PAM Support (pam_duo) | Duo Security there’s a list of options you can add to your pam_duo.conf config file. You’ll see the autopush configuration option in that list.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-04-2021 11:36 AM
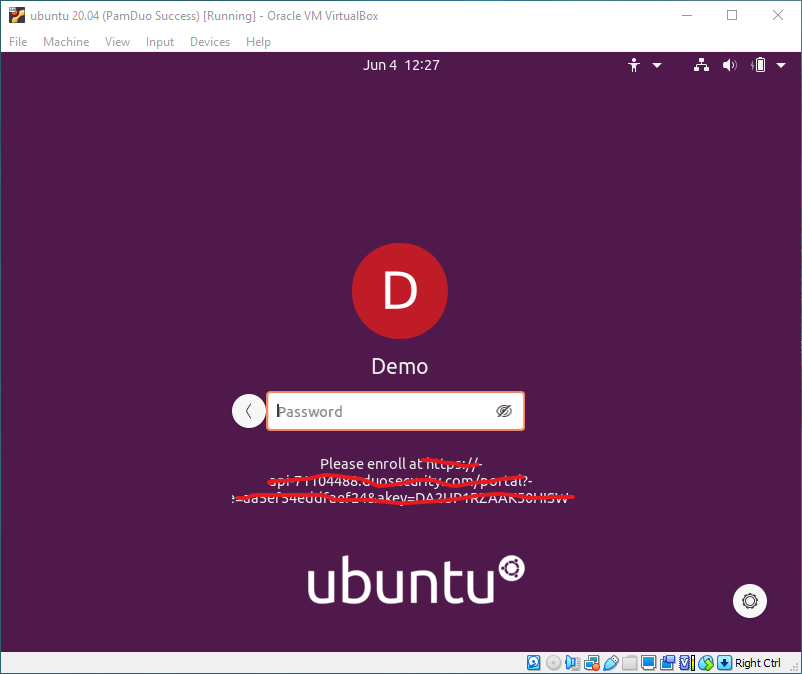
I have found a way to implement Duo with password for my User account.
I followed this guideline and seemed to work: How do I enable pam_duo to use passwords instead of public key authentication?strong text
I created a new user account and set the password. However, it prompts me to enroll the user with a given link. Unfortunately I can’t access the link from the login screen. I have tried to copy the link to enroll from my host machine but was not able to load the page. It resulted in an error.
How can I enroll new user accounts?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-07-2021 09:13 AM
-
Try to SSH in as that user, and you should be able to copy that enrollment URL from your terminal.
-
If you can’t SSH in, create the user in the Duo Admin Panel and add a 2FA device to that user, they try to log in to the Ubuntu desktop.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-07-2021 10:00 AM
Thank you, I was able to enroll the user from my account.
I have ran into another issue. I tried to access the Demo account and it shows this error:
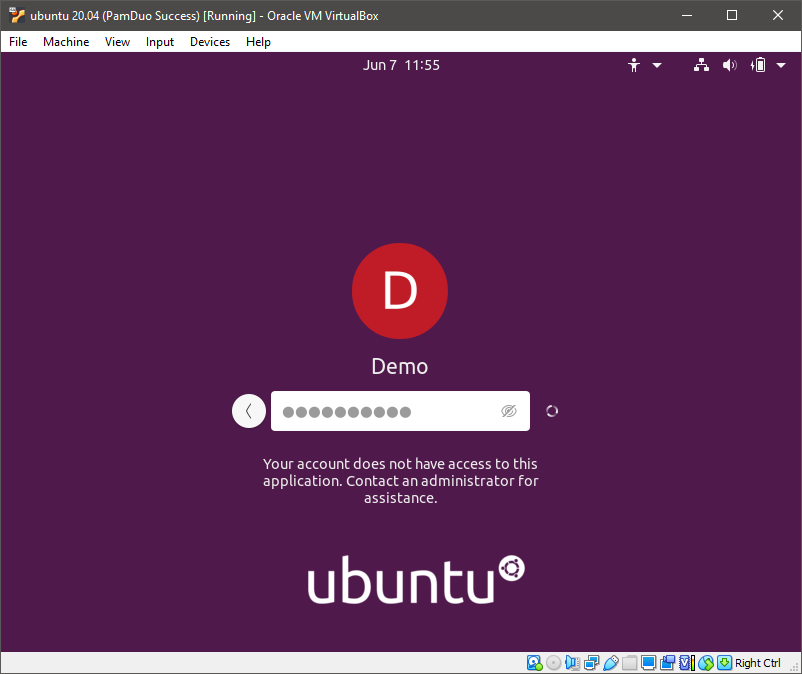
When I enrolled the Demo user, I enrolled with the same device as my default user… Could it be that each Linux user is limited to one Duo Account?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-17-2021 01:26 PM
The device to user limit and the user to device limit in Duo is 1:100 for both.
Did you configure permitted groups restrictions on your Duo Unix application in the Admin Panel? Is the Demo user a member of that permitted group in Duo?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-21-2021 11:51 AM
Sorry for the late reply. But yes, I was able to configure the permitted group restrictions on my Duo application.
I have another scenario. Is it possible to have a user that utilizes multiple computers, yet use the same device to authenticate him/herself whilst using one device for authentication.
eg. User A has an account on Computer A & B. Can User A authenticate his account on Computer A & B using one device?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-21-2021 12:04 PM
Yes, devices are attached to users only, not users AND endpoints, so a Duo user can authenticate to any application for which they are permitted using the same device, as long as the device type is permitted for those applications.
User A has an account on Computer A & B. Can User A authenticate his account on Computer A & B using one device ?
Yes, if User A exists in Duo with Phone A, and User A is permitted to log into the Duo applications installed on Computer A and B, User A can log into Computer B and authenticate with Phone A.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide