- Cisco Community
- Technology and Support
- Security
- Duo Security
- Protecting Applications
- Ubuntu Repository Access Denied
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Ubuntu Repository Access Denied
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-27-2018 06:15 AM
I seem to be running into trouble accessing the Ubuntu repo as given in the duounix documentation - https://duo.com/docs/duounix.
It says to create /etc/apt/sources.list.d/duosecurity.list with the following contents:
deb http://pkg.duosecurity.com/Ubuntu xenial main
Done.
Then execute the following shell commands:
curl -s https://duo.com/APT-GPG-KEY-DUO | sudo apt-key add -
Done.
apt-get update && apt-get install duo-unix
And here is where I hit some trouble. I get
Err:1 http://pkg.duosecurity.com/Ubuntu xenial InRelease 403 Forbidden [IP: 52.84.35.187 80] E: Failed to fetch http://pkg.duosecurity.com/Ubuntu/dists/xenial/InRelease 403 Forbidden [IP: 52.84.35.187 80] E: Some index files failed to download. They have been ignored, or old ones used instead.
So I am at a loss. What is going on here? Anyone else seeing this? Is there another repo I am unaware of?..
- Labels:
-
Unix and SSH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-27-2018 07:54 AM
I attempted to reproduce this on both Xenial and Precise and didn’t run into your issue.
Are you on a 32bit or 64 bit Xenial server?
As a test are you able to download the deb directly?
$ wget http://pkg.duosecurity.com/Ubuntu/dists/xenial/main/binary-amd64/duo-unix_1.10.0-0_amd64.deb
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-27-2018 08:07 AM
I am on a 64 bit Artful Aardvark server, actually. However, I don’t see how that would cause a problem with a Xenial repo.
I can download the deb directly, and that is how is ended up installing it, but I would love to figure out why I cannot do it through the repo.
Am I really the only one with this problem? If so, I can live with the direct download.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-27-2018 08:10 AM
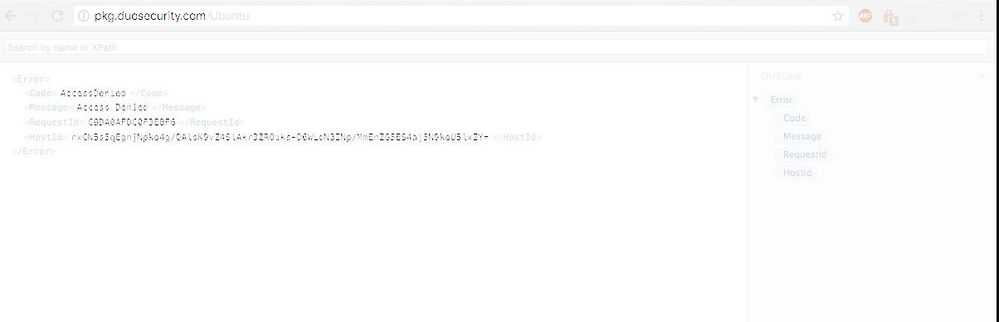
even going there in a browser gives me an error:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-27-2018 10:22 AM
So far you’re the first to report this with Artful Aardvark. We have seen one similar issue with a Debian distro that we failed to reproduce and the customer dropped off so we couldn’t continue troubleshooting.
We typically don’t release packages for the non LTS releases so I’m not entirely sure how compatible downloading a 16.04 package on 17.10 is but I wonder if that’s causing issues.
One other hunch that we might want to explore is double checking that the gpg key downloaded correctly. If that key isn’t present I believe it’s possible apt-get will have errors.
When you ran the curl and then apt-key add commands what was the output? Did it say OK?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-27-2018 11:15 AM
Well, I completely understand not updating for a non-LTS release and perhaps that has something to do with it. In which case, I can wait until the next Ubuntu LTS to try again.
The curl command DID return “OK”, yes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-27-2018 01:41 PM
So we just did some more testing on this with 17.10 and it appears that there is something different about how they do package management that breaks with our current system at pkg.duosecurity.com
We will do our best to make sure we fix this for 18.04 so definitely check back in when that hits.
Thanks for using Duo!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-27-2018 04:47 PM
Will do. Thanks for looking into it!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-15-2018 08:16 AM
I have this same problem. I think it stems from how you’re handling non-existent files. The apt tool is trying to fetch an InRelease file (an inline-signed Release file, which can be used in addition to the Release and Release.gpg pair), and when it attempts to fetch that file, Duo’s repository server is returning a 403 Forbidden, rather than a 404 Not Found.
In Ubuntu 17.10, apt prefers using the InRelease file, but apt will fall back to the Release/Release.gpg combo if the InRelease file is not found. The Duo server, however, is not telling apt that the file is not found – the server is telling apt that it is forbidden from accessing it. This seems to be due to a blanket policy on the Duo server to return a 403 Forbidden for any URL that does not exist, rather than a proper 404 code.
I do not know if the reason this happens is because of a change in 17.10’s apt or a change on Duo’s side to the repository configuration to always return 403 Forbidden for any non-existent resource. Either way, if Duo starts returning a 404 Not Found for all non-existent resources (like the InRelease file), everyone’s apt fetches will start working. Alternatively, Duo could provide an InRelease file. I think Duo should make at least the first change because a) it’s proper HTTP handling and b) customers on Ubuntu 17.10 (and maybe older versions) are not getting any automated updates to the duounix code.
Note:
The issue with the customer with a Debian distro was probably related to a newer Debian distro that also supported the InRelease file. Given the age of Duo’s packages, they were probably deployed before the InRelease file was preferred for use.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-16-2018 02:02 PM
Thanks for taking the time to explain this! I had suspected that it had something to do with a change to the way apt was grabbing from repositories, but I didn’t think about the 403 vs 404 workaround.
That seems like a relatively easy fix on our side. I’ll get this tracked internally so we can assess if it works and if there’s any other concerns to take into account.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-26-2018 04:11 AM
Hi, not sure if related, but some firewalls, e.g. Sophos XG declares the pgp key as malware:
2018-04-26 09:41:13Malwaremessageid=“08001” log_type=“Anti-Virus” log_component=“HTTP” log_subtype=“Virus” status="" fw_rule_id=“1” user="" web_policy_id=“13” policy_name="" virus="" url=“http://pkg.duosecurity.com/Ubuntu/dists/xenial/Release.gpg” domain=“pkg.duosecurity.com” src_ip=“192.168.110.200” src_country=“R1” dst_ip=“13.32.222.67” dst_country=“USA” protocol=“TCP” src_port=“46342” dst_port=“80” bytes_sent=“180” bytes_received=“517” user_agent=“Debian APT-HTTP/1.3 (1.2.26)” status_code=“500”
not only for duo also for e.g. keyserver.ubuntu.com:
2018-04-26 12:33:52Malwaremessageid=“08001” log_type=“Anti-Virus” log_component=“HTTP” log_subtype=“Virus” status="" fw_rule_id=“1” user="" web_policy_id=“13” policy_name="" virus="" url=“http://keyserver.ubuntu.com/pks/lookup?op=get&options=mr&search=0xD320D0C30B02E64C5B2BB2743766223989993A70” domain=“keyserver.ubuntu.com” src_ip=“192.168.110.200” src_country=“R1” dst_ip=“91.189.89.49” dst_country=“GBR” protocol=“TCP” src_port=“38632” dst_port=“80” bytes_sent=“229” bytes_received=“1063” user_agent="" status_code=“500”
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-03-2018 05:17 AM
Now that a new LTS release is available, will you be updating the repo and the install instructions on Duo Unix - 2FA for SSH with PAM Support (pam_duo) | Duo Security to reflect Bionic?
Thanks,
Matt
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-06-2018 02:48 PM
Any updates on support for Bionic?
-Sam
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-16-2018 12:08 PM
Hi all!
Sorry for the delay on all of this.
We were able to update the missing InRelease file to return a 404 instead of a 403.
Bionic support is on the way, but not released yet! We are hoping the next release of Duo Unix will have it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-28-2018 07:30 AM
Just to close gaps on all of the threads on this topic.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide