- Cisco Community
- Technology and Support
- Security
- Duo Security
- Managing Devices
- Palo Alto GlobalProtect is not prompting feild for Passcode or Hardware token when using DUO as Radi...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-12-2020 11:31 PM
Hi we have MFA based Palo Alto GlobalProtect VPN. we use DUO as our radius auth which when successfully authenticates directly sends out mobile push by default it doesn’t prompt for Hardware tokens or passcodes. the Authentication profile/method on DUO portal allows Harwdare token,passcode,push…etc. but when authenticating we only get a push on the PAN globalprotect agent on the ENd point.
can any one help me to get the prompt for passcode input field as well
Solved! Go to Solution.
- Labels:
-
Managing Devices - General
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-13-2020 01:48 PM
You do need to restart the Duo proxy service to pick up the config change. It should take less than a minute to cycle but it does mean nobody could log in during that time.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-13-2020 06:28 AM
Hi @sch,
If you take another look at the guidance in the Test your Setup section of the Palo Alto RADIUS Duo instructions, it shows you how users can opt for passcode authentication by appending the passcode to the password with a comma, like password,123456.
If you’d like an explicit prompt instructing users to pick a factor or enter a passcode, you can switch from [radius_server_auto] to [radius_server_challenge] which will not perform automatic push, and requires that the user input a device selection or a passcode to continue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-13-2020 09:09 AM
Does that setting needs to be performed on DUO gateway server right?
Also the append option with comma ","separator does that work out with Hardware tokens as well
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-13-2020 09:31 AM
THIS APPLIES TO YOUR CURRENT RADIUS AUTO CONFIG:
You can append any valid passcode type to the password. It can be a passcode from an OTP hardware token, or an SMS passcode received from Duo, or an YubiKey passcode, or a passcode generated by Duo Mobile, etc.
THIS ONLY APPLIES TO SWITCHING CONFIG FROM RADIUS AUTO TO CHALLENGE:
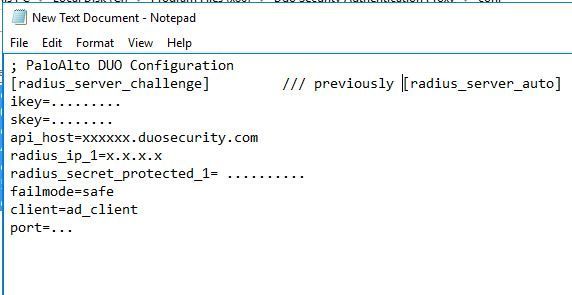
What do you mean by “Duo gateway server”? If you mean the Duo Authentication proxy server, yes, you would make that change by updating the authproxy.cfg file on the Duo Authentication Proxy and cycling the service. So if you currently have something like this in your cfg:
ikey=<your ikey>
skey=<your skey>
api_host=<your api_host>
radius_ip_1=5.6.7.8
radius_secret_1=radiussecret1
client=ad_client
port=1812
failmode=safe
You would update it to look like this:
ikey=<your ikey>
skey=<your skey>
api_host=<your api_host>
radius_ip_1=5.6.7.8
radius_secret_1=radiussecret1
client=ad_client
port=1812
failmode=safe
Keep in mind that RADIUS challenge mode precludes use of both autopush and passcode append.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-13-2020 01:05 PM
Thanks Kristina also does once i change authproxy.cfg to use from [radius_server_auto]` to [radius_server_challenge]. do i need to restart the services on the Duo Auth proxy server does that have any implicit down time of any sort or its just seamless after the change.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-13-2020 01:48 PM
You do need to restart the Duo proxy service to pick up the config change. It should take less than a minute to cycle but it does mean nobody could log in during that time.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-14-2020 11:41 AM
Thanks Kristina,
that radius challenge did the trick.
how ever i have small question
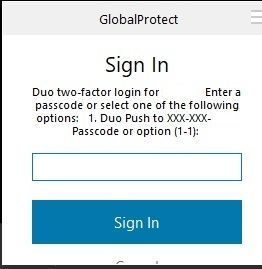
my account has option for Duo passcode, hardware Token in the Duo Portal. but the prompt only showed me only one option [1] i am attaching a snap of what i get for prompt. I tried using the command
“prompt_format=console” as well
is there a way or method to customize the message in that prompt challenge.
Also can we write a condition of sort saying that if you dont get any response by x sec fall back to radius_auto from radius _challenage.
Thank for all the help
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-14-2020 02:55 PM
my account has option for Duo passcode, hardware Token in the Duo Portal. but the prompt only showed me only one option [1] i am attaching a snap of what i get for prompt
It says “Enter a passcode or select one of the following…” That “Enter a passcode” text covers any type of passcode.
is there a way or method to customize the message in that prompt challenge
No, there is no way to customize the content of this message, other than to use the prompt_format option to determine whether the proxy tries to show full text or abridged text.
Also can we write a condition of sort saying that if you dont get any response by x sec fall back to radius_auto from radius _challenage.
No.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide