- Cisco Community
- Technology and Support
- Security
- Duo Security
- Managing Devices
- Newbie: 2 Users on 2 Devices with Duo Mobile & Yubikey
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-11-2020 01:53 PM
Hi there,
I’m checking out if Duo is the correct solution for a company I administer.
Successfully I registered my Duo-Admin-User and user A of MacBook A with Duo and the Duo Mobile/Duo Push.
Then I enrolled a second user (B) who (mainly) uses MacBook B with DUO, too. And for ease of testing added the same phone for this user B in the admin panel.
Additionally I want to protect login to MacBook B with a hardware token. It’s a Yubikey 5 which I also succesfully registered with DUO.
It works ok, but I would like to understand, how & why! ![]()
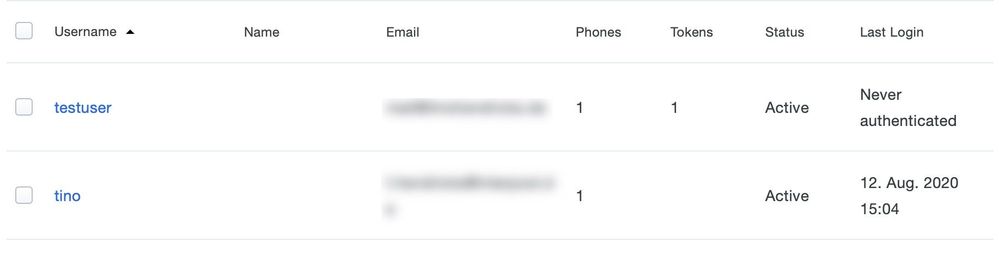
- Different from MacBook A this MacBook B never uses Duo Push due to lack of network connection during the early login process. Therefore this user still has “Never authenticated” in his details. Why is this?
- I was expecting the user B to show up in the list in Duo Mobile, just like the Admin user and user A. But it’s not. Is that normal? Should/Can I add it manually?
- How was MacBook B “informed” that this special Yubikey is the right one?
Sorry for dumb questions, I really tried to find the information somewhere else, to no avail.
Thank you very much!
Tino
Solved! Go to Solution.
- Labels:
-
Managing Devices - General
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-14-2020 06:12 AM
Not for Macs, no, just for Windows. Please contact your Duo account exec or Duo Care customer manager if you have one, or Duo support, to support the feature request for offline 2FA on Macs.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-12-2020 03:10 AM
Now I tested: I can log in to MacBook A (which never was in contact with the Yubikey before) with the Yubikey inserted without any question from DUO.
Obviously I’m missing something.
Clarification is greatly appreciated.
Tino
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-13-2020 06:44 AM
To Duo, 2FA authentication devices are associated with users.
Any user that exists in Duo with an associated 2FA device (a phone, a hardware token, a YubiKey, etc.) can log in to any Duo application by default.
If you create 10 Duo users and they all have a 2FA device attached, all 10 of those users could log into MacBook A or MacBook B with Duo.
To your specific questions:
Different from MacBook A this MacBook B never uses Duo Push due to lack of network connection during the early login process. Therefore this user still has “Never authenticated” in his details. Why is this?
A Duo user shows “Never authenticated” until that user performs an online 2FA login.
I was expecting the user B to show up in the list in Duo Mobile, just like the Admin user and user A. But it’s not. Is that normal? Should/Can I add it manually?
The Duo Mobile account list is is per Duo customer account. Once the phone is activated for use with a single user within that Duo customer account, it is essentially activated for any user in that Duo customer account that you associate with that phone. It is correct that you do not see two entries for the same Duo customer account in Duo Mobile after associating the phone with two Duo users in that account.
How was MacBook B “informed” that this special Yubikey is the right one?
Assigning the YubiKey to User B in Duo means that User B can use that same YubiKey to log in to any Duo application, as 2FA devices are attached to the Duo user, not to the system where a Duo client application is installed.
If you want to enforce a 1:1 relationship between a Duo user and a given MacBook (preventing User A from using Duo 2FA on MacBook B or User B from using Duo 2FA on MacBook A) there is a way to do this with the Permitted Groups application option, where you create a Duo group, put the user you want using the Duo application in the group, and then restrict access to that Duo application to members of that group. I don’t recommend this as it doesn’t scale well at all. If you don’t want User B to log on to MacBook A (or whatever) it is much easier to just not have a MacOS login for User B on MacBook A in the first place.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-13-2020 07:55 AM
Dear Kristina,
thank you so much for your extensive reply!
Thanks for making clear that devices are associated with users, not i.e. Applications or Access Devices.
One thing is still unclear: The Yubikey is not associated with user A “tino” (as you can see), still I can bypass the (offline) login on MacBook A with it.
Any more ideas who to do this correctly?
The goal is of course to have an online and offline savvy 2FA method for every individual user and 2 admins.
Thanks in advance
Tino
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-13-2020 08:16 AM
If the MacBook has no connectivity to the Duo service during login then it is subject to the fail mode setting you specified when you installed the Duo for Mac Logon application Should fail open. If you said true, then if the Duo application cannot contact the Duo cloud service at logon then it allows the user to bypass Duo authentication and log in. If you set that to false then no user can log on if the MacBook can’t contact Duo.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-14-2020 05:47 AM
Kristina, thanks again.
So it means there is no offline login possible secured with Yubikey associated with DUO.
That’s a pity.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-14-2020 06:12 AM
Not for Macs, no, just for Windows. Please contact your Duo account exec or Duo Care customer manager if you have one, or Duo support, to support the feature request for offline 2FA on Macs.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide