- Cisco Community
- Technology and Support
- Security
- Duo Security
- Protecting Applications
- Migrating from 365 mfa to Duo - When does the cutover happen?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Migrating from 365 mfa to Duo - When does the cutover happen?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-15-2021 03:59 PM
We currently have mfa running in our 365 tenant but we’re looking to migrate to Duo. I have successfully rolled out our RDP mfa with Duo and also have my on premise Access Gateway up and running. When I federate my domain, will that break the current mfa setup or does it only break when the user becomes federated? I’m asking because I would like to roll this out a few users at a time rather than an entire tenant.
Reading the 365 Documentation it makes me think the switch happens when the domain becomes federated.
Once you federate a custom domain your Microsoft Online tenant with Duo Access Gateway, all Microsoft 365 applications will redirect those federated users to Duo Access Gateway when they sign in, while cloud-only (non-federated) users continue to log in using the Microsoft online sign-in form.
We use locally installed versions of Outlook and Teams in my environment. Since both of those applications use 365 to authenticate, will the Duo mfa be added to that login?
- Labels:
-
Microsoft
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-16-2021 06:27 AM
Hi @opsteam,
Glad to hear you’re using Duo!
Unfortunately, when switching modes such as from “managed” mode to “federated” mode in Microsoft 365 this impacts all users within that domain.
If you have more than one domain in your Microsoft 365 account it might be good to start with the smaller domain to see how the changes will take effect.
Local versions of Outlook and Teams will also be prompted for SSO once federation occurs for users within that domain.
If you have not already rolled out Microsoft 365 with the Duo Access Gateway, I’d actually recommend you take a look at using Microsoft 365 with Duo Single Sign-On. This is our newer and more preferred way to integrate with M365 when doing SSO.
Duo SSO is our newer cloud-hosted SAML identity provider where we handle the web server side of things. We also have a more integrated setup with Microsoft 365 which allows for things like Azure Hybrid-Join and InTune to work better.
Definitely let us know if you have any more questions!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-16-2021 06:39 AM
Thank you @jamie ! I had a feeling it would change it for everyone when I federated the domain. Not a big deal though. I’ll get my rdp rolled out first so my users are familiar with the duo mfa push and schedule a time to convert our tenant for everyone.
What would be the benefit of using the on prem Access Gateway? I’m looking add mfa to my workstations, laptops, 365 tenant, and Salesforce for now. Does it make sense to have an on prem Access Gateway at all for those scenarios? Is it just needed as a way for Duo to connect to my local AD? Now that I think about it more, we’re a hybrid environment. Would it be better to have Duo connect to my AD via Azure AD? I apologize for dropping so many questions so fast.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-16-2021 06:48 AM
The benefit of the Access Gateway or Duo SSO is that they act as a SAML IdP that can be used to protect any applications that support SAML authentication for signing in.
Both the products put Duo MFA in front of every single authentication which allows you set unique authentication policies per application. An example of that might be is that you might allow most of your applications to use the “Remember Me” functionality so they don’t need to MFA every time they hit a new application but for a sensitive application like payroll, you can require that users MFA every single time they authenticate.
The value of Duo SSO is that we host all the web parts in the cloud and you can get Duo SSO to connect up to your local AD by using a Duo Authentication Proxy. This means that you aren’t opening up any inbound ports into your network and you don’t have to host a webserver in your DMZ.
Duo SSO does support allowing you to integrate with both traditional AD or a SAML IdP (like Azure AD) but I should note that if you want to protect Microsoft 365, there is a requirement that you use traditional AD to do so because of some limitations that Microsoft 365 requires for federation.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-16-2021 06:59 AM
So it really boils down to whether I want to manage the gateway in my DMZ or use Duo servers. From what I understand there is no added cost to use the hosted option, is that correct?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-16-2021 07:09 AM
That’s correct! You can also manage all Duo SSO settings in the Duo Admin Panel instead of having to log into the Access Gateway’s local admin console.
All paid editions of Duo include Duo SSO for free.
I will add that Duo SSO is where we are spending a lot of our development time. We just released a new feature Expired AD Password Resets with a lot more features currently in progress ![]()
Duo Passwordless when released will also require Duo SSO as a prerequisite.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-16-2021 12:36 PM
Interesting. What are the chances that Duo SSO will eventually be a paid feature?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-16-2021 12:53 PM
I can’t speak to the future but have no knowledge of plans to change that. Since Duo SSO was released it has been included in all paid editions of Duo.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-19-2021 12:59 PM
I think I migrated my very last Duo Access Gateway customer this week to Duo SSO (I call it Duo Central). I can’t see me ever deploying Duo Access Gateway again.
I would recommend you use Duo SSO over Duo Access Gateway.
From my experience, when you enable Duo for federation with office 365, those users already logged into Office 365 continue to remain logged in (I’m guessing they’ll stay logged in till their token expires). New authentication attempts go to Duo.
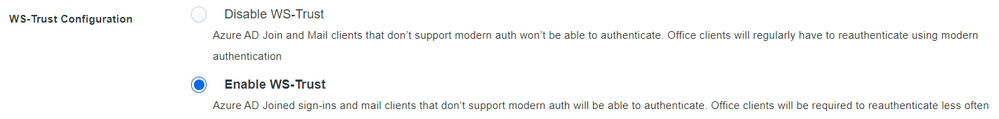
One more tip. Enable WS-Trust. It says it is only needed for thick clients that don’t support modern authentication. This is wrong. You will have constant grief if this setting is not enabled with Microsoft Office installed on desktops.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-19-2021 01:12 PM
That’s what I’m going for. I did get my Access Gateway up and running but everything we’re going to put behind the Duo mfa is cloud based. It doesn’t make any sense to keep this box running at this point. I’m just waiting on approval to remove it now. I appreciate the WS-Trust tip! That would have been a headache for my team.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide