- Cisco Community
- Technology and Support
- Security
- Duo Security
- Protecting Applications
- KEMP LoadMaster (load balancer) and DUO Auth Pxy
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
KEMP LoadMaster (load balancer) and DUO Auth Pxy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-04-2018 12:54 PM
Anyone have experience in successfully implementing the Duo Security Authentication Proxy behind a KEMP LoadMaster (load balancer) appliance array ?
We are attempting to move from proof-of-concept to production deployment that will include HA for the auth pxy service. All the pieces are in-place for the HA and each of the HA hosts can individually accept connections and complete the MFA authentication requests. However, the VIP connection does not work on our Kemp Loadmaster 3600 array and that VIP settings options were changed to resolve without success.
This support document was followed >> https://help.duo.com/s/article/authentication-proxy-availability?language=en_US
- Labels:
-
Authentication Proxy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-08-2018 01:27 PM
Is it the inbound auth request to the IP address assigned to the virtual service in front of the Authentication Proxy servers that isn’t working, or the connection from the Kemp virtual server to the Authentication proxy “real servers”?
Looking at https://support.kemptechnologies.com/hc/en-us/articles/203861485-Virtual-Services-and-Templates it seems like you’d create a virtual service VIP for your incoming authentication (you didn’t mention if you’re setting up Duo for RADIUS or LDAP, but specify the same port used for your incoming auth requests e.g. RADIUS 1812, etc.), and be sure and when you create this to use IP or Active Cookie persistence).
Next add a real server entry for each of your Duo Authentication Proxy servers, again using whatever port you configured for your authentication requests.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-09-2018 11:52 AM
Our KEMP analyst has made small changes for the VIP from TCP to UDP. We are now seeing some improvement in this issue. We are now getting mobile device app Approve / Deny push request but the Approve answer does not look like it gets sent back to complete the authentication and eventually the connection fails. Some clarity on how the Duo Pxy Auth requests get passed around between on prem servers and DUO cloud would be helpful.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-09-2018 03:24 PM
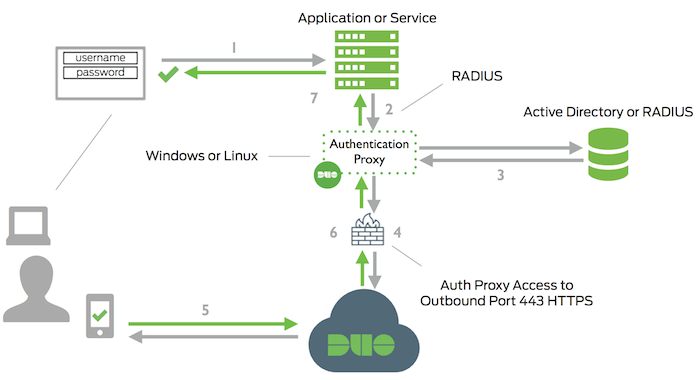
From Two-Factor Authentication Using RADIUS | Duo Security
Sounds like you’re stuck at step #6. If you enable debug logging on your Authentication Proxy servers and examine the output, do you never receive a response back after the POST to your Duo API host? Does your firewall permit inbound connectivity from duosecurity.com (or at least from your API hostname api-xxxxxxxx.duosecurity…)?
This is heading beyond the scope of a community post, so I suggest you contact Duo Support or your SE/SE team for ■■■■istance. That way we can review your debug logs with you, check our server-side logs, and perform other in-depth troubleshooting steps.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: