- Cisco Community
- Technology and Support
- Security
- Duo Security
- Managing Users
- Feature request: Bypass Mode
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Feature request: Bypass Mode
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-20-2020 08:39 AM
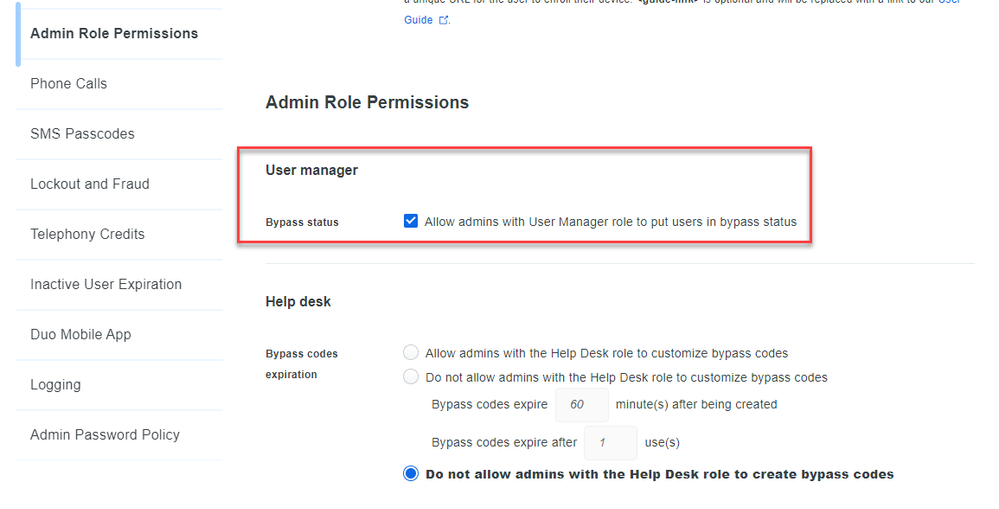
Please, please could we get the option to deny the permission for admins with the “User Manager” role to set users to bypass mode? Or at least a radial button in the Duo Admin Portal under Settings to DISABLE the option of Bypass Mode altogether?
We have many systems administrators in our organization, each responsible for a branch of the organization. They need to be able to manage the users under their branch (hence the User Manager role). However, we have a strict enterprise policy of not allowing any user to be able to bypass Duo. They can get a temp bypass code no problem but we don’t want them to be able to bypass mfa.
For now our workaround is to use a Splunk integration which triggers a script to reset a user to Active based on a Duo bypass mode event. Sometimes this can take a few minutes to execute the workflow and reset the user back to ACTIVE and that window of time is too long for our desired security posture.
Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-26-2022 11:11 AM
I couldn’t agree more. Please make this a feature. I would like to have the option to not allow some of our admins, user administrators and help desk folks to NOT be able to put people into bypass. It’s their “easy fix” for situations which they don’t know how or don’t want to resolve. I would rather they dealt with the issue, create a bypass code, or issue a hardware token temporarily.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-29-2022 10:00 AM
Thank you for sharing your thoughts. To file an official feature request, please reach out to the Duo support team or your account executive or customer success manager (if you have one).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-29-2022 11:42 AM
Kristina,
I have raised this request with our customer success manager. I posted this 2 years ago in the hopes of gaining more eyes on the feature request from other customers as well. This is still a problem for us and Duo customers.
-Buster
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-02-2022 11:06 AM
Raising awareness is a good idea, and if other customers see this and agree with the ask they should also contact Duo via the aforementioned channels to give support to the feature request.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-22-2022 03:07 PM
I do not see any mention in the release notes but is this a new feature available now in the Duo Admin portal? It appears that we can now enable/disable this ability for the User Manager role, this is a big deal for us!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-22-2022 03:25 PM
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide