- Cisco Community
- Technology and Support
- Security
- Duo Security
- Duo Release Notes
- Duo Release Notes for September 14, 2018
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 09-14-2018 07:10 AM
Hello everyone! Here are the release notes for the most recent updates we’ve made to Duo.
You can subscribe to notifications for new release notes by following the process described here. If you have any questions about these changes, please comment below.
New features, enhancements, and other improvements
New granular operating system (OS) policy features
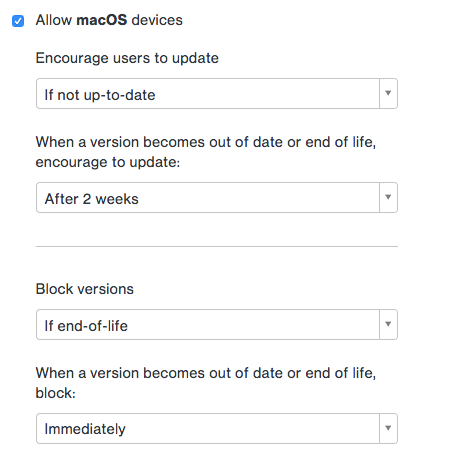
- Our OS policy controls for Duo Access and Duo Beyond Editions have been expanded and improved with more granular controls.
- OS policy can be set to target latest, up-to-date, end-of-life, and specific versions.
- “Encourage users to update” and “Block versions” are independently configurable.
Duo Admin Panel changes
- New dashboard styling and functionality.
- The dashboard of the Duo Admin Panel now displays:
- Telephony credits (for admins with the Owner or Billing roles)
- Out-of-date endpoints and change in that number month over month
- Inactive user count
- The dashboard of the Duo Admin Panel now displays:
- We have removed the numerical counts from the left-hand sidebar.
- If you navigate to “2FA Devices”, you will still see counts displayed next to the appropriate link.
- Application properties pages now have a “Select” button next to the integration key, secret key, and API hostname. Note that you must copy the selected text after selecting it in order to paste it.
- Fields and buttons in Trusted Endpoints Management have been updated to “Copy” buttons and fields to improve functionality.
New Duo Admin SAML Single Logout
- Single Logout allows administrators to be automatically logged out of the Duo Admin Panel after logging out of their identity provider. Single Logout is enabled by default.
- Single Logout is currently supported with AD FS, Azure Active Directory, PingOne, PingFederate, and Shibboleth.
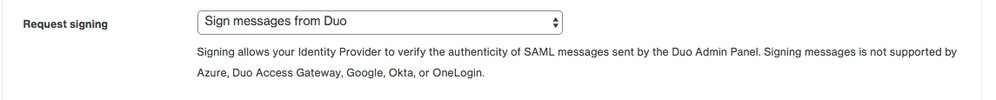
New Duo Admin SAML Message Signing
- Administrators can now configure the Duo Admin Panel to sign its authentication requests (used in the Single Sign On flow) and logout responses (used in Single Logout flow). This allows the identity provider to verify the authenticity of these messages from Duo. This can be enabled via the Admin Login Settings page.
- Signing messages is currently supported with AD FS, PingOne, PingFederate, and Shibboleth.
Miscellaneous changes
- Improved error messages when creating and updating administrator passwords using Admin API.
New and updated applications
Duo Authentication Proxy 2.10.0 released
- Added a new flag to authproxy_passwd.exe that allows you to encrypt all the passwords and secrets in the configuration at once.
- Fixed a bug in the Authentication Proxy Connectivity Tool that caused us to report an incorrect time drift.
- Added 2FA factor used to the SIEM digestible log output (authevents.log).
- Simplified example content in the authproxy.cfg file shown at first use.
Duo Mobile for iOS 3.23.1 released
- Small tweaks to improve landscape support.
- Miscellaneous improvements and bug fixes.
- New App Store screenshots to better describe Duo Mobile to new users.
Duo Mobile for Android 3.23.1 released
- Duo Mobile works with Android Pie (9).
- Notification badge support. You can now long-press on the Duo App icon to check for pending login requests on supported devices.
- Miscellaneous improvements for increased security and better accessibility.
- Modernization of our Android code. There will be no further updates for Android Lollipop (5.0). This follows our end of support for Android 5.0 in April, 2018.
Added Atlassian Cloud as an application to the Duo Access Gateway
- You can now protect your Atlassian Cloud services when using the Duo Access Gateway with Atlassian Access.
Updated Amazon Web Services SAML integration
- Our SAML Amazon Web Services application has been updated to support protecting accounts that run in Amazon Web Services GovCloud.
Added CyberArk Privileged Account Security Solution WebSDK integration
- This new configuration from CyberArk uses Duo’s WebSDK.
Bug fixes
- Fixed a bug that caused Duo Push authentications to time out if a user switched between certain Duo-protected applications and the Duo Mobile app on iOS 11.3 or later.
- Fixed a bug in the Duo Admin Panel whereby pressing enter while the search bar was focused caused the page to refresh.
- Fixed a bug in the Duo Admin Panel whereby syncing a single user who exists in multiple domains could cause the user to be set to a “Disabled” status in Duo.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
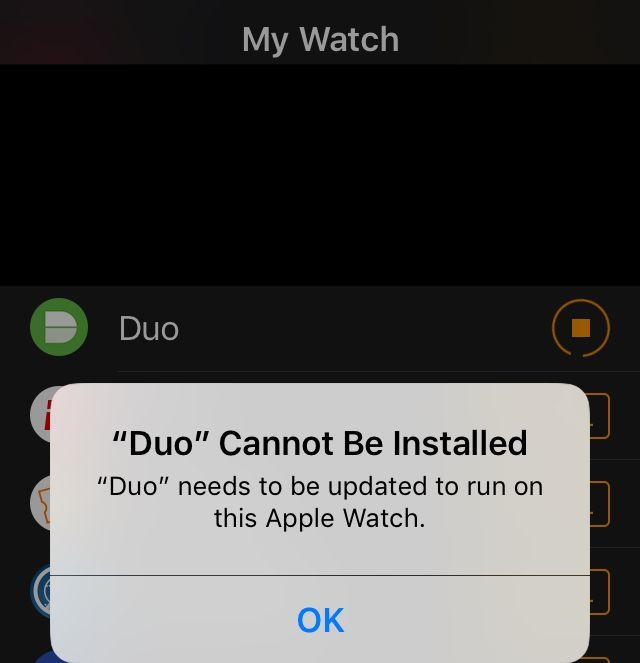
Per the attached screen image, I am unclear why the installation error message is present:
-iOS SE device running OS12 is active with latest version of Duo Mobile app 3.23.1.3 (to access third-party account codes, etc)
-Paired Apple Watch Series 3 has Duo Mobile watch app running, originally installed under Watch OS 4, upgraded and still running under Watch OS 5
-A newly Paired Apple Watch Series 4 running Watch OS 5 will not permit installation of watch version of app (3.23.1.3).
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
For anyone else who might encounter the issue bota describes, Duo’s Taylor McCaslin was able to troubleshoot this via Twitter: https://twitter.com/timbusbota/status/1045126396476092417?s=21
In summary, bota unpaired the old device and then power cycled the phone and watch. The issues then went away.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: