Hello everyone! Here are the release notes for the most recent updates we’ve made to Duo.
You can subscribe to notifications for new release notes by following the process described here.
Features, enhancements, and other improvements
U2F tokens
- Duo Free edition customers can now use U2F tokens at the Duo Prompt.
- Duo MFA edition customers can now opt in to use U2F tokens via the Settings page in the Duo Admin Panel.
- Note that Duo Access and Duo Beyond edition customers could already use U2F tokens prior to this update. Their experience will not change.
Labs Features in the Duo Admin Panel
- The Labs Features program in the Duo Admin Panel has been retired. The Labs Features section was only visible to Duo MFA edition customers prior to this update.
- Duo MFA edition customers who previously participated in this program will no longer see the Labs Features page under the Settings section in the Admin Panel.
- The only feature that remained under Labs Features was the “Allow the use of U2F tokens” checkbox. That option is now located on the Settings page under Authentication Methods.
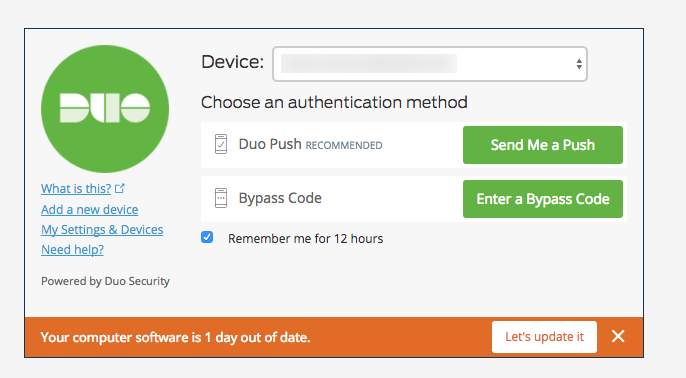
Out-of-date remediation via the Duo Prompt
- The Duo Prompt now shows the second out-of-date endpoint remediation page (which appears after a successful two-factor authentication) when the user’s software is at least one week out of date. This warning will also only appear once a day. This is to provide a better end user experience with software like Google Chrome that updates frequently.
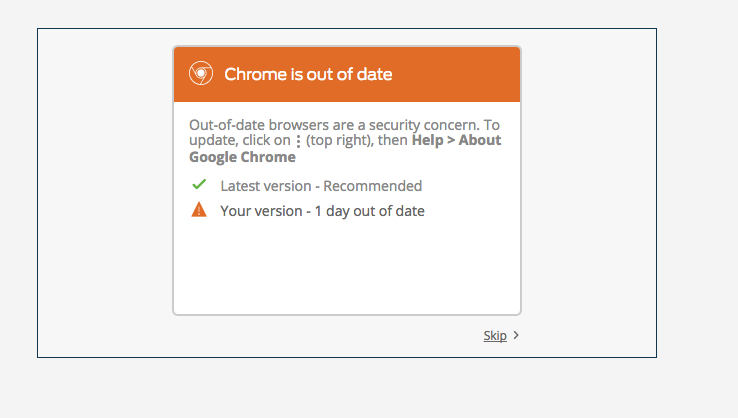
The initial warning banner is unchanged and will still appear at the bottom of the Duo Prompt.
Improved Trusted Endpoints Mac script
- We released a new version (v2.5) of our Trusted Endpoints Mac script for JAMF, generic Mac integrations, and manual Mac enrollment integrations.
- The new script:
- Has better logging.
- Solves an issue that could cause the duo-auth keychain to become permanently locked.
- Better detects and fixes misconfigurations to the system settings, including:
- Chrome plist policy to automatically select a certificate.
- Safari’s Identity Preference that automatically selects our certificate.
- Keychain’s ACL list that whitelists app to use our certificate (like Slack).
- LaunchAgent, which automatically unlocks the keychain on boot.
- Password being out-of-sync between the login keychain and duo-auth keychain.
- Missing private key.
iOS device detail page in the Duo Admin Panel
- When an iOS device is not a Trusted Endpoint, we no longer indicate that it lacks a certificate on that device’s page in the Duo Admin Panel. We now say it is not enrolled in your trusted environment.
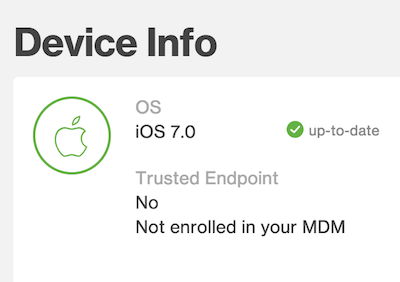
- When an iOS device is a Trusted Endpoint and has a certificate, the device’s page will indicate as such and be accompanied by additional information.
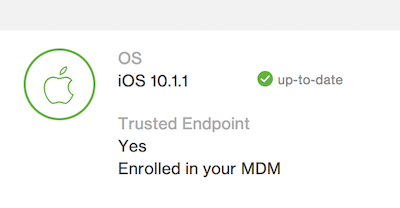
- If an iOS device is a trusted endpoint but doesn’t have a certificate, the page will indicate that it is enrolled in your trusted environment.
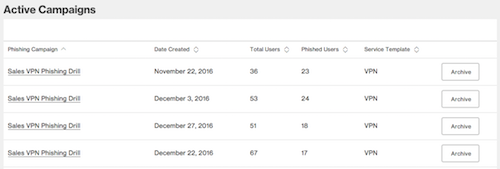
Archiving phishing campaigns in the Duo Admin Panel
- Users can now “archive” phishing campaigns, which will hide the campaign from the Active Campaigns table.
Mobile-first enrollment via the Duo Prompt
- When enrolling on a mobile device via the Duo Prompt, the platform selection page is now skipped and the appropriate platform (iPhone, Android, Windows Phone) is automatically selected and the user will proceed directly to the phone number page.
- Note that this only works for platforms that Duo Mobile supports.
Default SMS passcode batch size in the Duo Admin Panel
- The default SMS passcode batch size, which is configured in the Settings page of the Duo Admin Panel, has been changed from 10 to 1 for new customers. Existing customers’ settings are not affected.
New and updated applications