- Cisco Community
- Technology and Support
- Security
- Duo Security
- Duo Release Notes
- Duo Release Notes for October 2, 2020
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 10-02-2020 06:13 AM
Hello everyone! Here are the release notes for the most recent updates we’ve made to Duo.
You can subscribe to notifications for new release notes by following the process described here. If you have any questions about these changes, please comment below.
What’s in this release?
New features, enhancements, and other improvements
- Announcing Public Preview for Duo Central
- New CSV Update Options for Directory-Managed Users
- Service Reliability Feature Addresses Authentication Latency Events
- Universal Prompt Progress Report Updates
- Improved Trusted Endpoints Workflow for Android
New and updated applications
- Duo Authentication Proxy Version 5.0.2
- Duo Mobile for iOS Version 3.39.0
- Duo Mobile for Android Version 3.39.0
- Webex ControlHub for the Public Preview of Duo Single Sign-On
Bug fixes
New features, enhancements, and other improvements
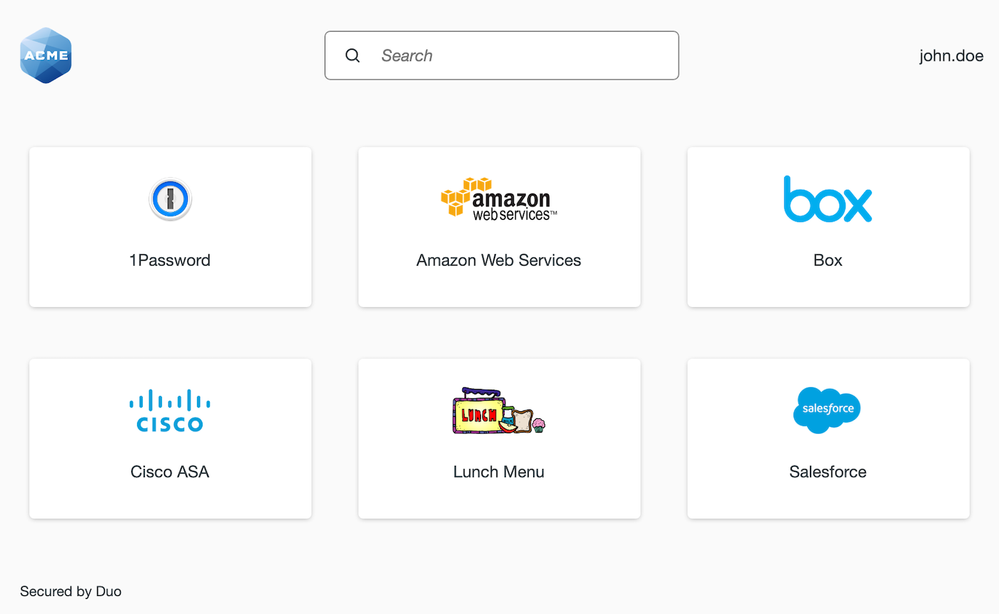
Duo Central, now in public preview, provides a single place for users to access applications
- Customers participating in the public preview of Duo-hosted Single Sign-On can now enable a new UI where end-users can access their applications from a single page. This portal is called Duo Central.
- Duo Single Sign-On and Duo Central can both be enabled and configured from the Duo Admin Panel by going to Single Sign-On in the left navigation.
- The public preview of Duo Central is available for all non-Federal customers on MFA, Access, or Beyond editions.
CSV import can now be used to update specific fields on users managed by Directory Sync
- The following fields can now be modified via CSV import for Duo users managed by an external directory (e.g. Active Directory or OpenLDAP):
- User alias attributes not managed by the external directory.
- Notes not managed by the directory.
- Phones can be added to users managed by the directory.
- A user’s status can be changed between Active and Bypass if the user has not been assigned a status of Disabled in the directory.
- Changes via CSV to any other fields for a directory-managed user, or to a directory-managed user’s group assignments, will be ignored. The UI message that appears after completing a CSV import will note that any changes made to directory-managed fields were ignored.
- In addition, the Administrator Actions log will report the number of directory-managed users that were updated (if any exist).
New service reliability feature will gate authentication requests in rare scenarios where an outage could occur
- If a Duo deployment experiences latency in authentications averaging 4 seconds, Duo will deny some new inbound authentication requests in order to preserve Duo’s service.
- This scenario occurs in rare cases and allows Duo’s service to clear the queue of authentication requests while avoiding an outage.
- In the event of an authentication latency issue, users will see an error message when trying to access the Duo Prompt or in Duo Mobile. Applications that use the Auth API will receive a standard 429 Too Many Requests error message.
- See this Duo Knowledge Base article for more information.
Updates to the Universal Prompt Update Progress report in the Admin Panel
- The Universal Prompt Update Progress report displays which of your applications will be capable of supporting the new Duo Universal Prompt. This report is currently visible only to customers with a Microsoft Azure Active Directory Conditional Access or Duo Single Sign-On application because these were the first two applications to receive back-end updates in support of the new prompt, which is currently under development.
- This report now displays a label for applications that support the prompt but are awaiting the release of back-end updates required to support the new prompt. This label reads “Waiting on App Provider.”
- The report now also links to Duo’s Universal Prompt documentation hub page.
Improved workflow for Trusted Endpoints device trust verification when using Android devices
- When performing a Trusted Endpoints check on Android where Duo Mobile is being used as the device verification tool, end-users will now be directed to manually open Duo Mobile if the app fails to launch after selecting “Open Duo Mobile” in the Duo Prompt. Previously, if Duo Mobile failed to open on an Android device in this context, a user could be blocked from completing authentication.
New and updated applications
Duo Authentication Proxy version 5.0.2 released
- No longer adds
Message-Authenticatorto RADIUS packets where it was not already present. - Fixed an issue preventing Authentication Proxy startup when using the
pass_through_attr_namesRADIUS setting. Note that thepass_through_attr_namesandpass_through_alloptions are only valid when used withradius_client; specifying these parameters for RADIUS server sections that make use ofad_clientorduo_only_clientprevents the Authentication Proxy service from starting.
Duo Mobile for iOS version 3.39.0 released
- Behind-the-scenes improvements and minor bug fixes.
Duo Mobile for Android version 3.39.0 released
- Behind-the-scenes improvements and minor bug fixes.
Improvements to Webex ControlHub for the public preview of Duo Single Sign-On
- The Webex ControlHub application for Duo Single Sign-On now supports uploading an XML metadata file to support changes made by Webex.
- Errors caused by duplicate usernames or aliases will now display more specific error messages to assist with troubleshooting, such as
"foo@example.com" is already an alias of user "joe@example.com". These more specific messages will appear if there is a conflict created when manually editing a user on the Users page of the Admin Panel, when making changes via directory synchronization, or when making changes via the Admin API. - Fixed an issue where user objects returned from Admin API phone-related endpoints did not include those users’ aliases.
- Removed the unused Service Provider Name field from the configuration page for Duo Single Sign-On for Generic SAML Service Provider.
- Fixed an issue where special characters were not rendering correctly in the Region dropdown field on the Admin Panel Settings page.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: