- Cisco Community
- Technology and Support
- Security
- Duo Security
- Duo Release Notes
- Duo Release Notes for March 30, 2018
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 03-30-2018 07:04 AM
Hello everyone! Here are the release notes for the most recent updates we’ve made to Duo.
You can subscribe to notifications for new release notes by following the process described here.
Features, enhancements, and other improvements
Protect SSH servers with Duo Network Gateway 1.3.0
- You can now protect SSH servers using Duo Network Gateway 1.3.0, which was released March 19, 2018.
- This allows you to remotely access your SSH servers by tunneling the connection through DNG using HTTPS. You can group access to a set of servers, after you’ve authenticated you’ll be able to connect all servers in that group. You might decide to group servers by level of security or by departments within your organization. Each group of servers can have its own policies.
- Learn more about protecting SSH servers with DNG in the documentation.
Trusted Endpoints now supports Sophos MDM for Duo certificate deployment to mobile devices
- Sophos MDM can now be used as a Trusted Endpoints mobile configuration. An administrator must have Sophos version 8.0 or higher deployed as their MDM to utilize it as a Trusted Endpoints configuration.
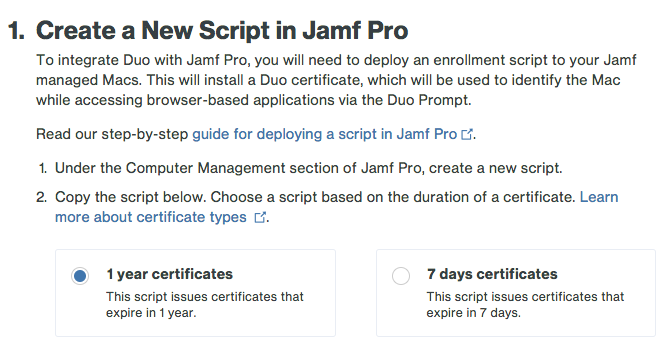
Trusted Endpoints now supports short-lived certificates
- When configuring a Trusted Endpoints integration, Duo administrators may now choose between using seven-day (short-lived) certificates and one-year certificates. This feature can help administrators ensure that their users are still in their management systems. This feature is available for all Trusted Endpoints integrations. Duo suggests using seven-day certificates if using Trusted Endpoints to protect Citrix clients or similar VDI environments.
Admin API now features new bypass code endpoints
- New endpoints for managing bypass codes with Admin API have been added.
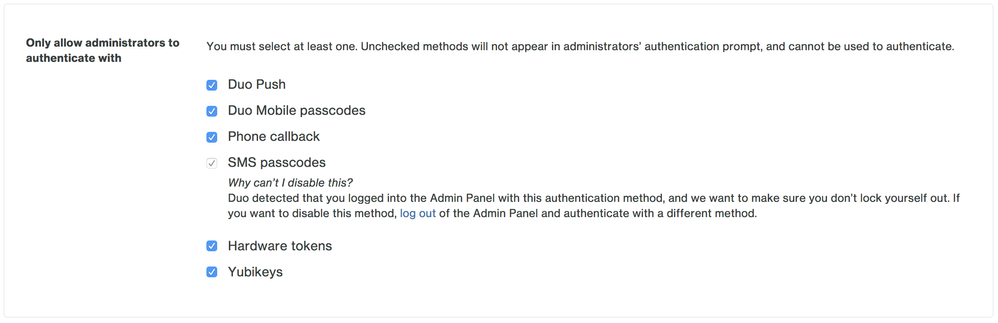
Improvements to Duo administrator factor restrictions setup
- When restricting Duo Administrator two-factor methods on the Administrator Login Settings page in the Duo Admin Panel, the methods the admin logged in with will be disabled with a message explaining that this is to prevent the admin from locking themselves out, along with how it can be disabled. Previously, attempting to disable this methods would always result in an error.
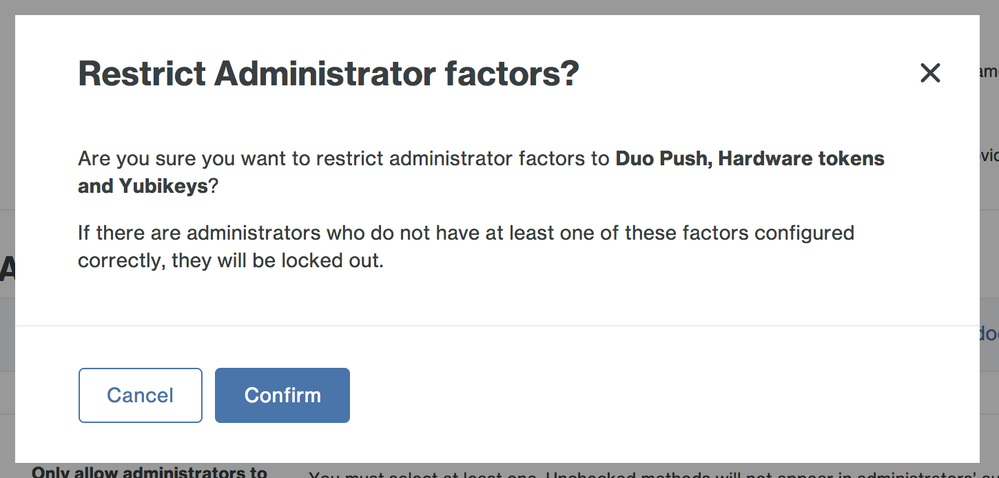
- When restricting admin methods on the Administrator Login Settings page, when an admin removes one or more methods and hits save, a confirmation dialog box will ask to confirm that the administrator to remove those factors. It also warns that they may be locking out some administrators.
New and updated applications
-
Duo Authentication for macOS 1.0.3 was released.
- It contains bug fixes for Active Directory accounts.
-
Duo Authentication Proxy for Windows 2.8.1 was released.
- Corrected issue with EAP and TLS 1.2 that affected NetMotion Mobility. Learn more in the Knowledge Base.
- Duo Network Gateway 1.3.0 was released.
- Includes SSH server protection feature described above.
- Includes UI improvements.
- Now requires Docker v1.12 and Docker Compose v1.10 at minimum.
Bug fixes
- Fixed a bug when using Trusted Endpoints, macOS 10.13, and Office 365 that would present users without certificates with a blank grey screen and prevent authentication when trying to access O365.
- Previously if a customer tried to use the Google Drive File Stream with an account protected via a U2F token, Google Drive File Stream would crash. This bug has been fixed. The solution was to disable the U2F option when attempting to authenticate a Google Drive File Stream user. Google Drive File Stream cannot use U2F.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
The https://dl.duosecurity.com/duoauthproxy-latest.exe link is still downloading version 2.7.0. When will it be pointing to 2.8.1?
Thanks!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
It won’t!
There is no need to install 2.8.1 unless you are using Duo with NetMotion Mobility 11 (per the linked article https://help.duo.com/s/article/4284). We don’t recommend that customers not affected by the NetMotion issue upgrade, which is why it is not the “latest” linked version.
Keep an eye out for version 2.9.0 of the Authentication Proxy (which will be released as “latest” for both platforms). ![]()
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Ah…OK! My mistake. Thanks for the clarification!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Does this address the Fall 2017 Creator’s update breaking RDP if using a Microsoft account?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Peter, this release did not address that issue. PatrickKnight’s most recent post in the thread you linked contains the most up-to-date information we have on the issue.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: