- Cisco Community
- Technology and Support
- Security
- Duo Security
- Duo Release Notes
- Duo Release Notes for March 15, 2019
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 03-15-2019 06:51 AM
Hello everyone! Here are the release notes for the most recent updates we’ve made to Duo.
You can subscribe to notifications for new release notes by following the process described here. If you have any questions about these changes, please comment below.
New features, enhancements, and other improvements
Touch ID can now be used as a second factor when using macOS and Chrome
- This new, easy-to-use biometric functionality utilizes WebAuthn, which helps reduce risks associated with phishing while making it easier for end users.
- End users can easily enroll Touch ID devices using the self-service portal in the Duo Prompt.
- You can control whether Touch ID can be used as a 2FA method with an Authentication Methods Policy. The default setting for new customers allows all of Duo’s authentication methods, but existing customers will need to enable WebAuthn authentication methods in their policy settings.
- Learn more about Touch ID and Duo’s plans for WebAuthn.
Security keys can now be used with Firefox
- You can now utilize security keys in Mozilla Firefox browser in addition to Google Chrome.
- You can control whether Security Keys can be used as a 2FA method in Firefox with an Authentication Methods Policy. The default setting for new customers allows all of Duo’s authentication methods, but existing customers will need to enable WebAuthn authentication methods in their policy settings.
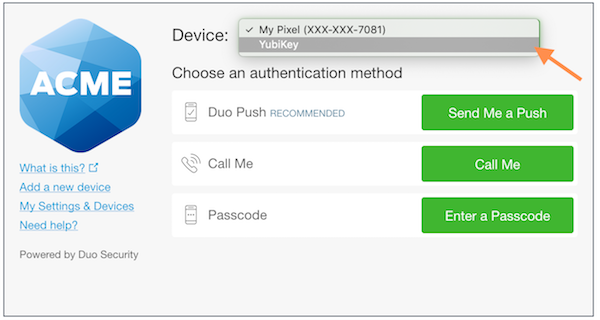
- Note that if you were using a security key with Chrome before this update, you will need to use it to authenticate once more in Chrome before you can use it with Firefox. Additionally, you will have to manually select your security key from the device drop-down list in the Duo Prompt.
Miscellaneous enhancements
- When the integration is changed or removed for Duo Restore for Duo Mobile, the integration and URL are now logged in the Administrator Actions log.
New and updated applications
Duo Mobile 3.25.0 for Android released
- The Duo Mobile app now implements Federal Information Processing Standard (FIPS) 140-2 compliant encryption for Duo Push notifications and for generating HOTP passcodes for Duo-protected accounts.
- Because of this update, the FIPS configuration setting in the Duo Admin Panel is no longer available. If you had enabled the “Require FIPS 140-2 encryption on Android passcodes” option before this change, then the setting will remain in effect for passcodes generated on Duo Mobile for Android versions older than 3.25.0. It had no effect on push notifications.
- Miscellaneous bug fixes and improvements for increased stability.
- Note that push notifications and HOTP passcodes in Duo Mobile for iOS are already FIPS 140-2 compliant.
Bug fixes
- When a Duo Administrator’s password is changed, all active sessions will be expired forcing them to log in to the Duo Admin Panel again.
- Fixed a bug that caused Admin API single-user syncs to Azure Active Directory to fail when username normalization was enabled.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Why can’t the iFrame detect if a YubiKey or Touch ID “device” exists and simply give you the blue banner like the existing security key functionality in Chrome? Is this a limitation of WebAuthn, the iFrame, the browsers, or something else? I think the way customers currently have to drill down is really going to stall adoption of these factors. Just curious if this is somehow only possible for browsers that support U2F.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi peesh23. I asked one of our engineers about this and they had this to say:
“A WebAuthn interaction cannot be automatically initialized from inside of an iframe. We encourage users to set their Yubikey/Touch ID as their default device in order to avoid switching to that device, should they choose. We are continuing to work on a solution for this so that WebAuthn interactions can be automatically initialized.”
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: