- Cisco Community
- Technology and Support
- Security
- Duo Security
- Duo Release Notes
- Duo Release Notes for February 28, 2020
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 02-28-2020 06:06 AM
Hello everyone! Here are the release notes for the most recent updates we’ve made to Duo.
You can subscribe to notifications for new release notes by following the process described here. If you have any questions about these changes, please comment below.
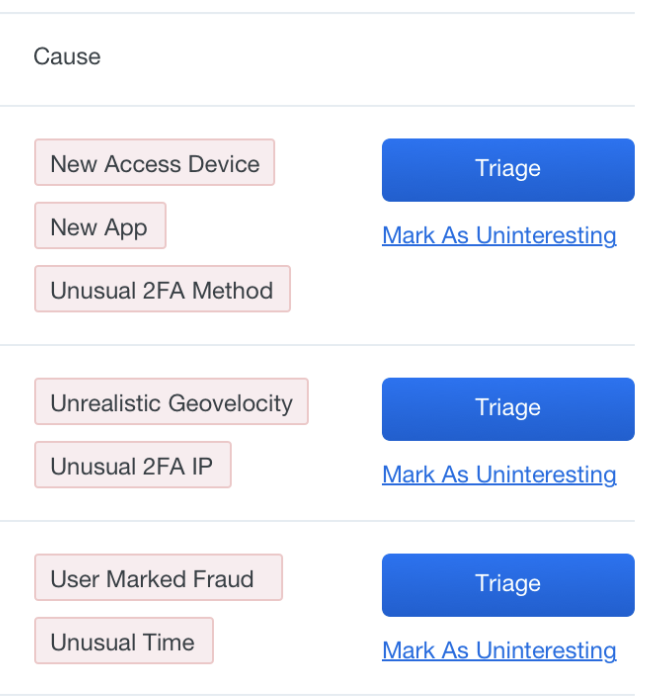
New public beta: Get behavioral security analytics with Duo Trust Monitor
Duo Trust Monitor is a security analytics feature that analyzes users’ historical Duo activity and telemetry data to identify risky or potentially insecure user behavior. It will soon be available in public beta.
Customers on Duo’s Access or Beyond editions interested in joining the public beta should reach out to their account representative.
New features, enhancements, and other improvements
Enhancements to Directory Sync
- Admins who do not have permissions to configure Directory Synchronization will no longer be able to see the Authentication Proxy entry in the sub-navigation.
- Duplicate attributes are no longer allowed across username and alias fields for synchronized Active Directory and OpenLDAP directories. For example, you cannot have “samaccountname” as the attribute for both username and alias 1.
- Sub-navigation links for Active Directory, Azure Active Directory and OpenLDAP pages will now be hidden on small screens to enable administrators to see more of the main content.
- Invalid groups in an Azure Active Directory will no longer prevent the directory configuration page from saving. For example, if a group that has been added to Duo via Azure is deleted in Azure, admins will still be able to save the directory settings in the Admin Panel.
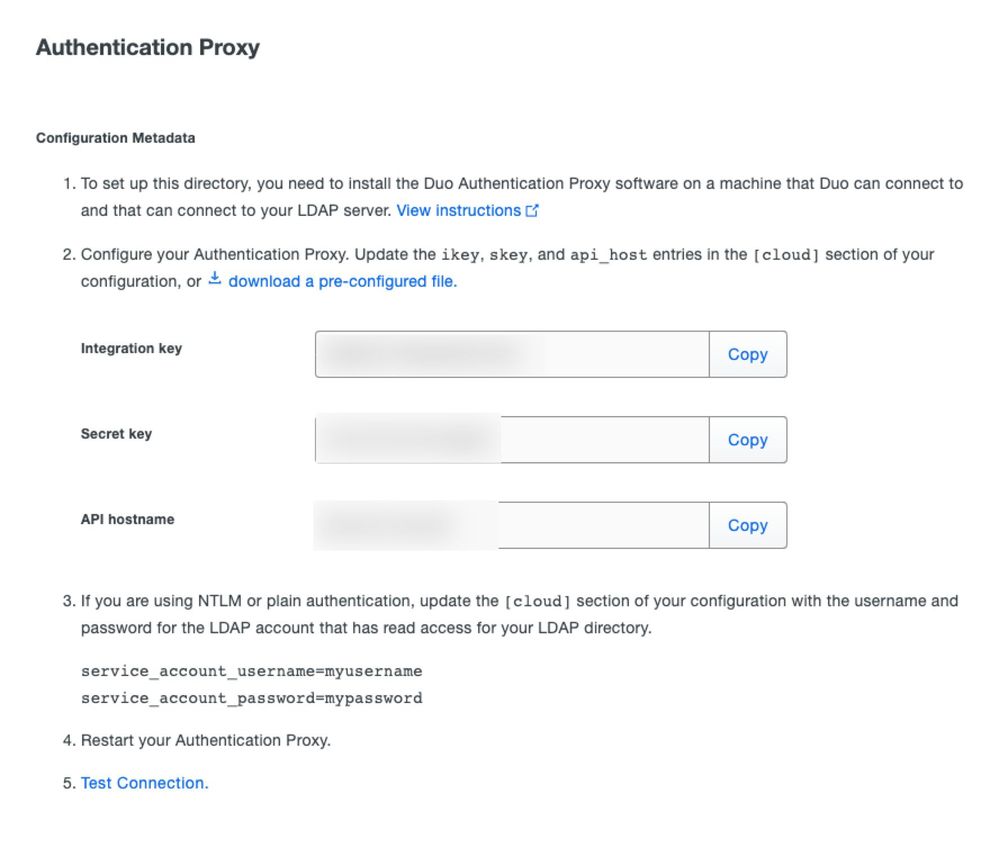
- Added additional instructions for configuring the Authentication Proxy using NTLM or plain authentication in both the Admin Panel UI and in the preconfigured file download provided to admins.
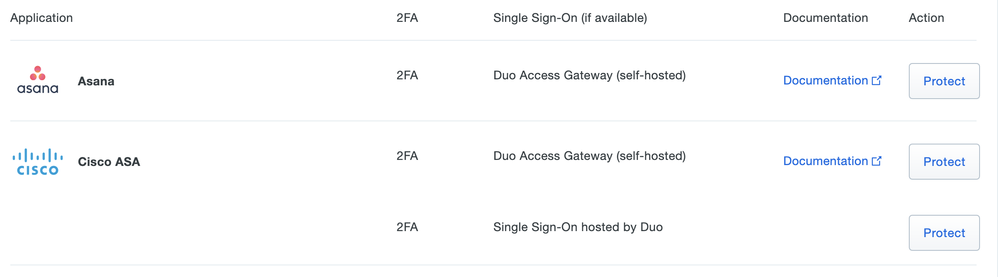
Single sign-on information now displayed on Protect an Application overview page
-
Added a column titled “Single Sign-On (if available)” on the Protect an Application overview page to help identify the method that will be used to protect an application.
New messaging for administrators logging into the Duo Admin Panel with Internet Explorer
- Added a message to the Admin Panel login screen encouraging admins using Internet Explorer (IE) to upgrade their browser to the most recent version of Chrome, Firefox, or Microsoft Edge. Previously, a message encouraging browser upgrade appeared only for users on IE 10 or below.
Update to Device Health Application and Windows Operating Systems policy definition
- When using a Device Health Application policy in tandem with an Operating Systems policy, a Windows 10 device is now considered “up-to-date” based exclusively on the latest security patch version.
- Previously, optional and preview updates that contained non-security fixes (known as “C” and “D” releases) were also taken into consideration when evaluating whether a device was up-to-date. These optional and preview updates are no longer considered to be more “up-to-date” than others by Duo’s service.
Timestamp format standardized across Authentication, Telephony, and Administrator Action logs
- The format of timestamps has been standardized to ISO 8601 for Duo’s Authentication, Telephony, and Administrator Action logs. This change will also be reflected in logs exported via CSV or JSON format, as well as logs retrieved through the Admin API.
- Standardizing the timestamp makes it easier to merge logs and filter events by time.
New and updated applications
Duo Network Gateway (DNG) 1.5.5 released
- Added support for Google Chrome version 80 SameSite cookie change.
- Updated the way Duo Network Gateway generates self-signed certificates to conform to macOS 10.15 requirements. Self-signed certs are used during initial setup of the DNG.
Duo Authentication Proxy 3.2.2 released
- Fixed a bug causing NTLM and SSPI authentications to fail in rare cases.
Bug fixes
- Directory Sync fixes:
- Disabled the ability to select groups in Active Directory or Azure Active Directory configuration pages while the directory is syncing or checking the connection.
- Added fix for preventing admins from creating or saving multiple Active Directory syncs with the same name.
- Fixed several UI rendering issues for Internet Explorer 11 that affected the way Directory Sync, Active Directory, and Azure Active Directory pages rendered in the Admin Panel.
- Fixed a documentation link on the Active Directory Sync page that incorrectly pointed to OpenLDAP documentation.
- Admin Panel Users page fixes:
- Fixed issue with the search input box in the Users table not holding cursor focus or resetting the user’s cursor mid-query in Internet Explorer and Microsoft Edge.
- Prevent a directory-synced user’s synced phone from being manually removed from a user’s account page in the Admin Panel, or when using the Admin API. Synced phones must be removed from the directory itself.
- Admin Panel Groups page fixes:
- Prevent admins with the Help Desk role from adding or removing users from groups.
- Admin Panel login screen fixes:
- Fixed a bug in the UI where the username and password fields were erroneously displayed above the two-factor authentication options during the “forgot password” login flow for the Admin Panel.
- Authentication Prompt fixes:
- Fixed issue where some Microsoft WebViews’ Flash software was misinterpreted as being out of date.
- Admin API fixes:
- Updated the HTTP status code from 500 to 400 when syncing a user from Active Directory through the Admin API and the Authentication Proxy or directory is unreachable. The status code is also now accompanied by an error message.
- Azure Active Directory sync fixes:
- Updated the wording of an email that is sent when an Azure sync is disabled and re-authorization is needed. The new wording clarifies that users with the roles of Owner, Administrator, or User Manager are all receiving the message because they have permission to re-authorize directory syncs.
- Admins whose permissions are restricted by Administrative Unit status will no longer receive sync-related error emails because the information is not actionable for them.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: