- Cisco Community
- Technology and Support
- Security
- Duo Security
- Managing Users
- Duo authentication proxy - how it works
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-17-2022 09:49 PM
Hello folks!
I’m totally new to Duo, but I’ve been working as an IT pro for quite a while now. Our organization is exploring the idea of implementing Duo MFA to domain-joined Windows Servers.
I’ve managed to set up a basic environment to initially test how Duo works and everything seems to work. Though I have questions around Authentication Proxy…
- From official docs (Authentication Proxy Reference - Duo | Duo Security) “The Duo Authentication Proxy is an on-premises software service that receives authentication requests from your local devices and applications via RADIUS or LDAP, optionally performs primary authentication against your existing LDAP directory or RADIUS authentication server, and then contacts Duo to perform secondary authentication.” - does this mean domain member servers with Duo agent no longer need Internet access?
- My initial setup of authentication proxy did not have [ad_client], and everything was working. So, I’m wondering what’s the difference if I add [ad_client]?
The ultimate objective I have in mind is when I roll out Duo to our production environment is to limit limit our servers connecting to the internet, if that’s possible through Authentication Proxy.
I’ve seen this What are the differences between [ad_client] and [radius_client] Duo Authentication Proxy configurations? so I think it’s possible, but I’m not really sure though.
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-02-2022 06:05 PM
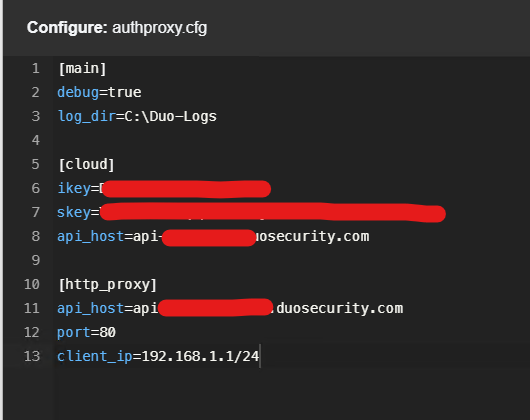
Hello @DuoKristina - sorry for the late response as I was away. I had another look, and I found the cause for the error. It was my fault ![]() - I double added the “api-” so my proxy was trying to reach “api-api-xxxxxx”.
- I double added the “api-” so my proxy was trying to reach “api-api-xxxxxx”.
After removing “api-”, it’s now working.
Thank you so much!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-19-2022 02:45 PM
Hello @akosijesyang, good to hear from you and thank you for posting!
There are a couple of different ways to respond to the questions you’ve raised, here.
First, about the Duo Authentication Proxy:
- The Authentication Proxy itself needs an internet connection in order to reach Duo for secondary authentication. Your domain member servers do not need an internet connection for the end-user authentication to work.
- With
[ad_client]in the config, Authentication Proxy verifies primary authentication with your on-premise Active Directory. You may get some mileage from this Knowledge Base article, see the numbered steps in the diagram.
However, you may want to consider the Duo Authentication for Windows Logon and RDP module to protect those logins. Duo Authentication Proxy wouldn’t be required for the Windows Logon integration, because Winlogon relies on the local OS for primary authentication.
Finally, if your servers with the Winlogon integration don’t have an internet connection either directly or through an existing HTTP proxy, the Duo Authentication Proxy can act as an HTTP proxy only for traffic communicating with Duo.
You may also add a registry entry that tells Duo Authentication for Windows Logon to direct traffic to an HTTP proxy such as the Duo Authentication Proxy.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-19-2022 06:07 PM
Hello @timshores - thank you for the response. I really thought my post was totally ignored ![]()
If my understanding is correct [ad_client] is only used by application who does not have native integration with Winlogon - so for Windows RDP, is it not required? (Which makes sense since the original pre-configured authproxy file I downloaded did not have that).
Yes, I’m using RDP as an application in Duo Admin portal, which I already configured some policies.
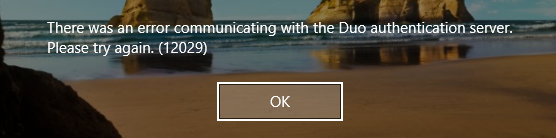
So, I did configure the settings mentioned here [Duo Authentication Windows Logon RDP: FAQ | Duo Security] (Duo Authentication Windows Logon RDP: FAQ | Duo Security), as you suggested. Though when I blocked Ports 80/443 from my edge firewall for member-server, I got an error:
My Duo authproxy server has internet connection, btw.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-20-2022 06:48 AM
If my understanding is correct [ad_client] is only used by application who does not have native integration with Winlogon - so for Windows RDP, is it not required?
Adding some more detail to @timshores’s previous answer…
Correct, [ad_client] is only used when you have also configured a RADIUS or LDAP server listener on the Duo Authentication server (radius_server_* or ldap_server_auto) and have a RADIUS or LDAP application pointing to the Duo Authentication Proxy for primary and secondary authentication.
Duo Authentication for Windows Logon deployments do not require installation of Duo Authentication Proxy on your network at all. But, if your Windows clients do not have direct internet connectivity to Duo’s cloud service and you do not already have an HTTP proxy for these clients to use, you could use Duo Authentication Proxy for this.
So, you are trying to use the Duo Authentication Proxy server on your network as the HTTP proxy for Windows clients with Duo Authentication for Windows Logon and have issues…
-
You configured the Windows system where Duo for Windows Logon is installed to use your Duo Authentication Proxy server as an HTTP proxy with registry entries, but did you also perform the corresponding config change at the Authentication Proxy (adding an
http_proxysection with the IP addresses or subnets of the Windows servers that will proxy the Duo authentication connection through that Authentication Proxy server)? You need to make both changes for the Windows clients to connect through the Authentication proxy server to Duo’s service. -
Does your Duo Authentication proxy server have direct internet connectivity or have you configured it to use an outbound web proxy too (with the
http_proxy_hostandhttp_proxy_portsettings in the[main]section? If the Authentication Proxy is using a web proxy to connect to Duo then it cannot also act as an HTTP proxy to other systems so they can connect to Duo. The Authentication Proxy requires direct outbound connectivity to Duo to act as the HTTP proxy for other hosts. -
If you have already checked 1 and 2, try enabling debug logging on the Authentication Proxy server and on the Duo Windows client, perform your test again, and go look at the debug output to see what is happening.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-24-2022 04:51 AM
Hello @DuoKristina
Sorry for not getting back sooner. I’m now getting new error from client machine
Here’s my auth proxy config btw.
Thank you for pointing this out - just configured them (auth proxy config and gpo for client)
You need to make both changes for the Windows clients to connect through the Authentication proxy server to Duo’s service.
Yes, auth proxy server has direct internet access
Does your Duo Authentication proxy server have direct internet connectivity?
This is what I’m getting…
<< removed image with customer-specific account information >>
If you have already checked 1 and 2, try enabling debug logging on the Authentication Proxy server and on the Duo Windows client, perform your test again, and go look at the debug output to see what is happening.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-25-2022 07:57 AM
Hi - I removed your log output screenshot because it contained some of your customer information in a non-redacted form.
The error message received was: Bad Proxy Request: Attempted connection creation to non approved host: <your duo api hostname> . This suggests that clients were trying to use the Authentication Proxy as an HTTP proxy to connect to a different API host than what was configured on the Duo proxy itself.
-
Is the
api_hostvalue in your[http_proxy]section of your authproxy.cfg the EXACT same API host value used to install Duo for Windows Logon on those Windows clients? -
Did you restart the Duo Authentication Proxy service after making changes to authproxy.cfg? A restart is required for changes to take effect.
If you check both of those points and still have issues I suggest you contact Duo Support to open a case.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-02-2022 06:05 PM
Hello @DuoKristina - sorry for the late response as I was away. I had another look, and I found the cause for the error. It was my fault ![]() - I double added the “api-” so my proxy was trying to reach “api-api-xxxxxx”.
- I double added the “api-” so my proxy was trying to reach “api-api-xxxxxx”.
After removing “api-”, it’s now working.
Thank you so much!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-03-2022 05:44 AM
Glad it was an easy fix.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-13-2023 08:39 PM
it's really helpful for your explanation with DUO proxy. Thank you so much.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: