- Cisco Community
- Technology and Support
- Security
- Duo Security
- Duo Release Notes
- D257: Duo Release Notes for Jan 20, 2023
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 01-20-2023 06:31 AM
Hello everyone! Here are the release notes for our most recent updates to Duo.
Public release notes are published on the Customer Community every other Friday, the day after the D-release is completely rolled out. You can subscribe to notifications for new release notes by following the process described here. If you have any questions about these changes, please comment below.
What’s in this release?
New features, enhancements, and other improvements
- Now in Public Preview: Duo Network Gateway API
- Operating Systems Policy Version will be Updated for Windows
- Duo Single Sign-On Log Now Includes Failed SSO Authentications
- New Duo Policy Defaults for Browser and Operating Systems Policies
- Duo Admin Panel Menu Improvements
New and updated applications
- Duo Network Gateway Version 2.2.0
- DuoConnect Version 2.0.4
- Duo Single Sign-On for Datadog
- Duo Mobile 4.32.0 for Android
- Duo Mobile 4.32.0 for iOS
Bug fixes
New features, enhancements, and other improvements
Now in Public Preview: Duo Network Gateway API
- Duo Network Gateway 2.2.0 and later may be configured and administered via the Duo Network Gateway API.
- Previously, Duo Network Gateway (DNG) configuration required either the DNG Admin UI or DNG Scripted Configuration.
- Now the Duo Network Gateway API lets administrators configure the DNG through a RESTful API with methods for creating, retrieving, updating, and deleting core configuration in the DNG, as well as configuration and management of DNG web, SSH, RDP, and SMB/file share applications.
Operating systems policy version will be updated for Windows
- Effective February 6, 2023, Windows 8.1 will be marked end-of-life for operating system policy purposes.
Duo Single Sign-On Log now includes failed SSO authentications
- The log, found in the Duo Admin Panel under Reports > Single Sign-On, now includes failed 2FA authentications where primary authentication was successful with Duo Single Sign-On.
New Duo policy defaults for browser and operating systems policies
- Browser policy defaults as of D257 will enable Warn users if their browser is out of date.
- Operating system policy defaults as of D257 will disable Allow Blackberry devices and Allow Windows Phone devices.
- Following the D256 general availability release of Duo policy defaults, Duo continues to roll out new policy defaults designed to give our customers a security posture that is resilient against trending attack patterns.
- As before, please note that the new policy defaults feature will not modify your existing policies.
Duo Admin Panel menu improvements
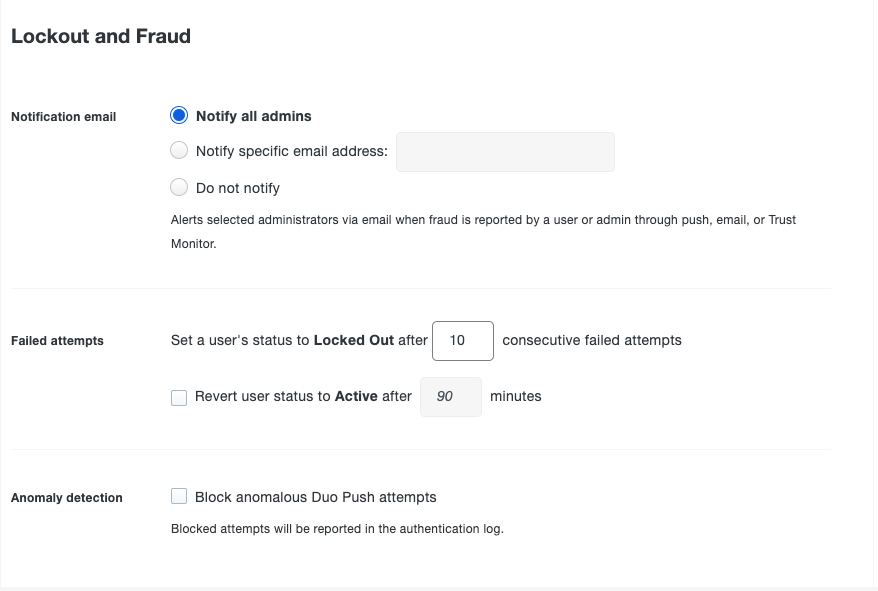
- Improved organization of Lockout and Fraud settings menu:
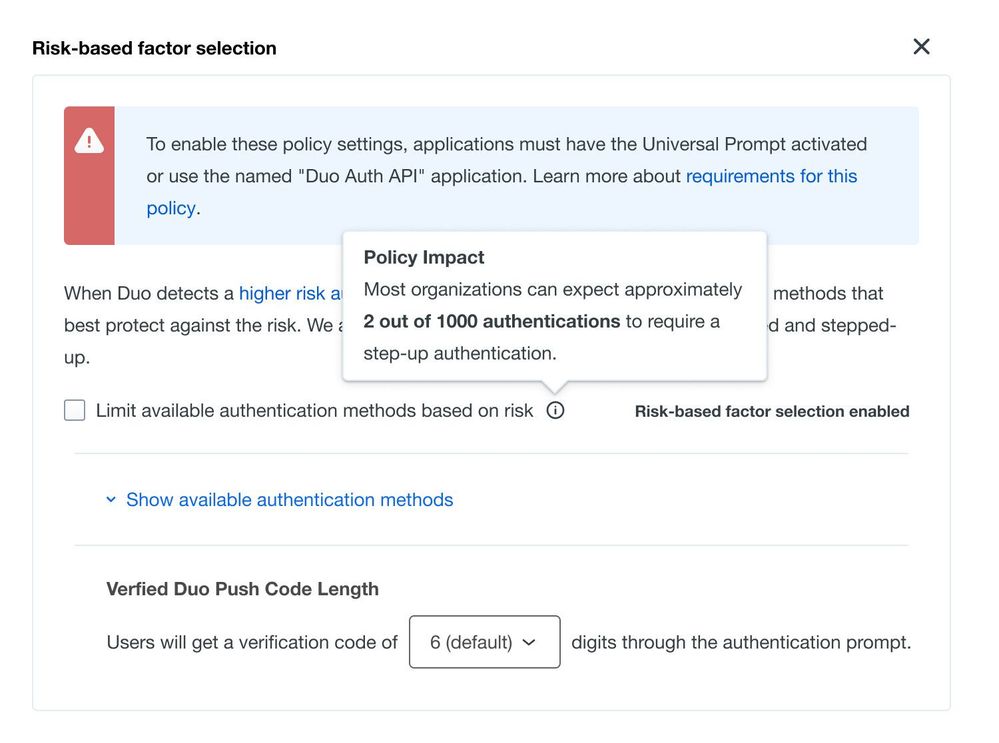
- A new tooltip in the Duo Risk-based factor selection policy builder menu describes Policy Impact and gives admins insight into how often most organizations could expect to step up.
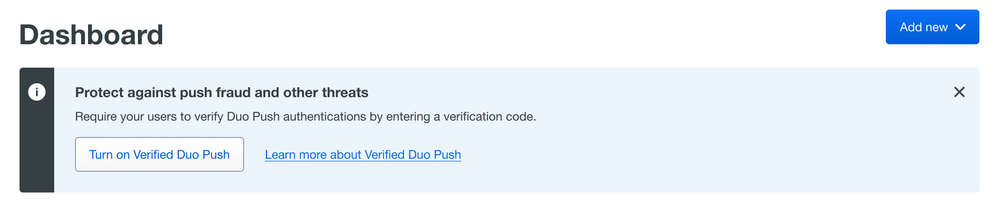
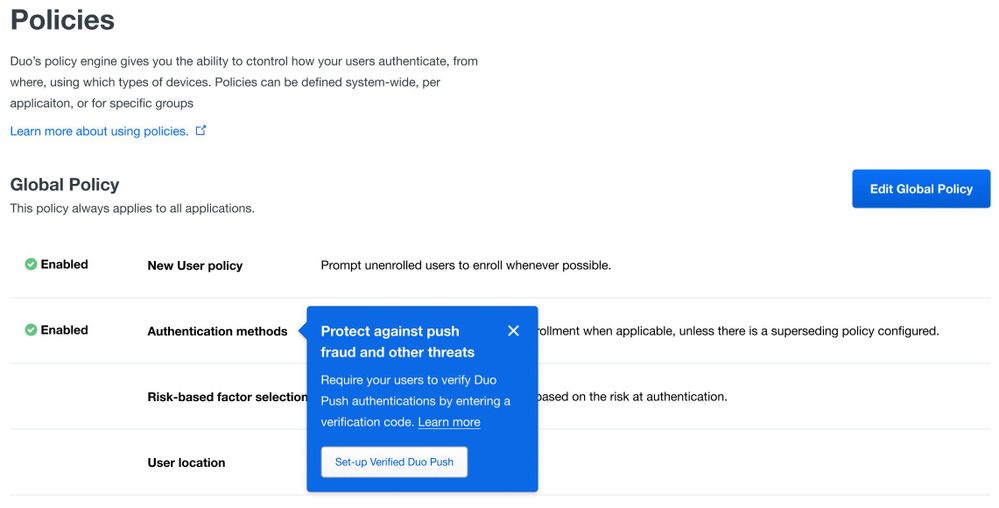
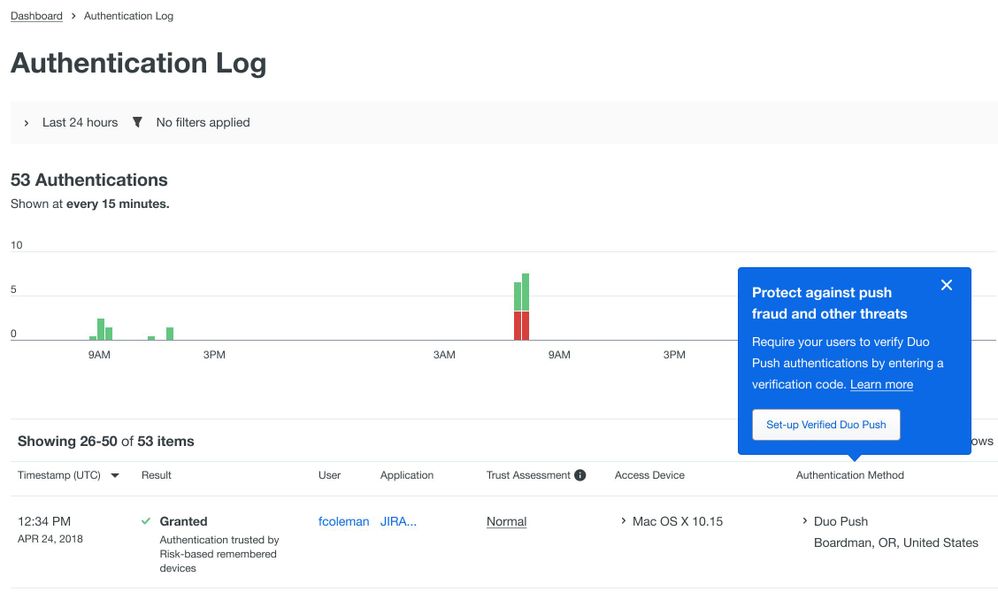
- A Dashboard banner and Authentication Log and Policies page simplify the option to turn on Verified Duo Push.
New and updated applications
Duo Network Gateway version 2.2.0 released
- Public preview of Duo Network Gateway API for DNG administration.
- General availability of SMB/File share access protected by Duo Network Gateway.
- Prevention of Server-Side Request Forgery (SSRF) attacks where an upstream DNS entry is pointed at the AWS metadata service at 169.254.169.254.
- Supports proxying upstream TLSv1.3 connections.
- Permits setting the maximum header size of a request to a value beyond the previously-fixed maximum of 8 KB via the DNG admin console and scripted configuration.
- Fixes an issue with setting a port for the external URL of a web application in DNG admin console.
- Fixes an issue where browsing to an SSH or Application relay application in a web browser would present an OpenResty page.
- Updated dependencies: Python to 3.9.6, PCRE to 10.40, libxml2 to 2.10.2, cryptography to 36.0.2, pyOpenSSL to 22.0.0, and libxslt to 1.1.37.
DuoConnect version 2.0.4 released
- Updated Go version used to compile DuoConnect to v1.19.1.
Duo Single Sign-On for Datadog
- There is now a named application to protect Datadog using Duo Single Sign-On, our cloud-hosted SAML identity provider.
- Reminder: Duo Access Gateway will reach end of life in October 2023. Please see the Guide to Duo Access Gateway end of life for more details. If you already use Duo Access Gateway to protect Datadog, try the DAG to Duo SSO application migration process.
Duo Mobile for Android version 4.32.0 released
- Do not prompt for autofill when performing verified push.
- Disallow device-to-device transfers on Android 12 and up. This was already restricted on earlier Android versions.
Duo Mobile for iOS version 4.32.0 released
- Miscellaneous bug fixes and behind-the-scenes improvements.
Bug fixes
- Duo Passwordless updated to allow enrollment of usernames with apostrophes.
-
Operating systems policy updated to prevent inappropriately blocked authentications. The new behavior is to skip macOS policy when the Duo Device Health application is not installed and the authentication has one of the following properties:
- A Cisco AnyConnect useragent parses as originating from macOS 10.15.17 or 10.16 (applies to VPN login).
- An unknown browser useragent parses as originating from macOS 10.15.17 or 10.16 (applies to protected application login).
- Updated Duo admin directory sync notification email timing to prevent email sent to incorrect admin user following a role change.
- Updated Duo Admin API user sync error that resulted when a directory username or email is updated during the sync.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: