- Cisco Community
- Technology and Support
- Security
- Duo Security
- Duo Release Notes
- D253: Duo Release Notes for Nov 11, 2022
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 11-10-2022 11:09 AM
Hello everyone! Here are the release notes for our most recent updates to Duo.
Public release notes are published on the Customer Community every other Friday, the day after the D-release is completely rolled out. You can subscribe to notifications for new release notes by following the process described here. If you have any questions about these changes, please comment below.
What’s in this release?
New features, enhancements, and other improvements
- Duo Passwordless Now in General Availability
- Verified Duo Push Now in General Availability
- Duo Trusted Endpoints Manual Enrollment with Device Health Now in General Availability
- Duo Risk-Based Factor Selection Now Includes More Informative Configuration Menus and Logs
- Duo Admin Panel Now Exports WebAuth & U2F Security Key List
- UX Improvements to Admin Directory Sync
- Duo Single Sign-On Error Page Now Displays an Error Trace ID
New and updated applications
Bug fixes
New features, enhancements, and other improvements
Duo Passwordless now in General Availability
- Available at no added cost to all Duo MFA, Access, and Beyond edition customers using Duo Single Sign-On.
- Passwordless General Availability includes a user-facing change: Passwordless enrollment with Duo Push enabled on the effective policy will require a single Verified Duo Push authentication during the end-user’s Passwordless Push enrollment flow. After the Passwordless General Availability rollout from November 3 to November 10, every end-user currently enrolled with Passwordless Push must complete a Verified Duo Push the next time they authenticate.
Verified Duo Push now in General Availability
- Available at no added cost to all Duo MFA, Access, and Beyond edition customers.
- By requiring end-users to enter a verification code to approve a Duo Push authentication request, Verified Duo Push adds security from push harassment and push fatigue attacks. It also provides improved fraud reporting from end-users by directing them toward the fraud report option in Duo Mobile when they receive unexpected Duo Push login requests.
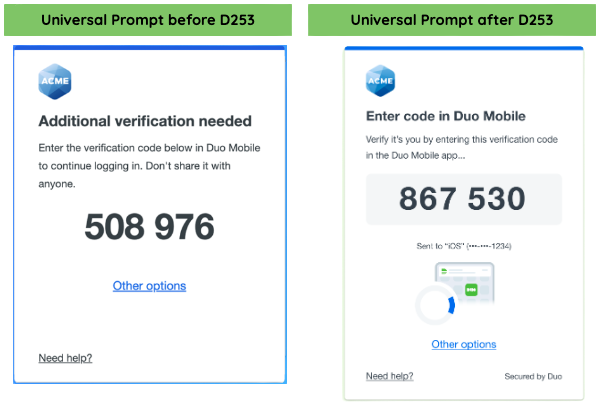
- Improvements to the information displayed by the Duo Universal Prompt after a user logs into an application protected by Verified Duo Push. Please note that these UI improvements have not been applied to the Verified Duo Push authentication required during a Passwordless Push enrollment flow.
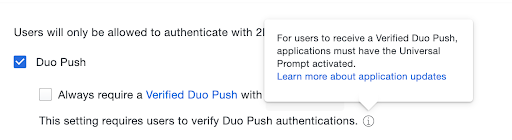
- The Authentication methods policy configuration menu now includes a tooltip describing the requirement.
Duo Trusted Endpoints Manual Enrollment with Device Health now in General Availability
- Duo Beyond edition administrators can now manually add or delete device identifiers in the Duo Admin Panel. These extend Trusted Endpoint policies to protected applications accessed by BYOD and vendor devices that are not managed by the enterprise mobile device management solution (MDM).
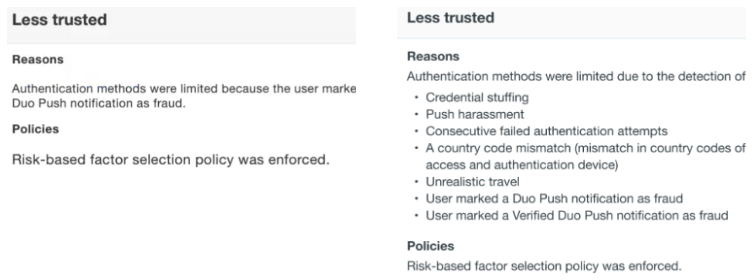
Duo Risk-Based Factor Selection now includes more informative configuration menus and logs
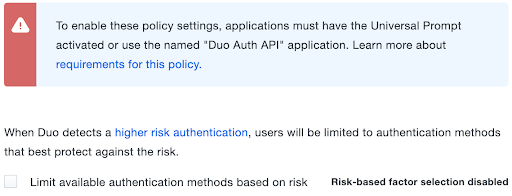
- The configuration menu used to enable Risk-based Factor Selection policy for an application now shows a banner describing supported integrations.
- The policy summary now includes a tooltip describing supported integrations.
- Authentication factor step-up events are now more verbose in the Duo Authentication Log.
Duo Admin Panel now exports WebAuth & U2F security key list
- WebAuthn & U2F security key list can now be exported to CSV, JSON and PDF file formats
UX improvements to Admin Directory Sync
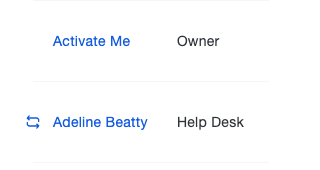
- Administrators with the Owner role who log into the Duo Admin Panel to manage Administrators will see a sync icon next to Duo Admins synced with Active Directory.
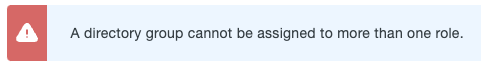
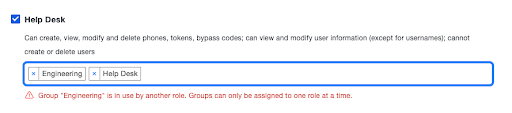
- Updated the Admin Directory Sync warning message when a given directory group is assigned to more than one role.
- Previous message:
- New message:
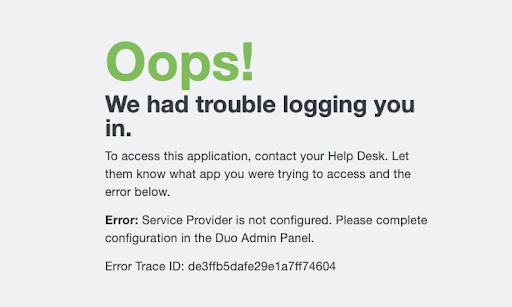
Duo Single Sign-On error page now displays an Error Trace ID
- Duo Support can use Error Trace IDs to track down related log events for faster and more systematic resolution of support issues.
New and updated applications
Duo Authentication Proxy 5.7.4 released
- Improved logging for LDAP timeouts.
- The Authentication Proxy Manager and connectivity tool now warn against use of ‘clear’ transport in ad_client with certificates specified.
- Removes the misleading no reply message in packet RADIUS error message to reduce confusion while troubleshooting authentication failures.
- No longer duplicates the proxy-state RADIUS attribute when both the RADIUS client and server configuration sections specify pass_through_all=true.
- The connectivity tool no longer exits prematurely when it fails to connect to a RADIUS server that is not running.
- Fixed an issue that could result in multiple redundant connections to the Duo SSO service in certain race conditions.
Duo Mobile for Android version 4.28.2 released
- New in Duo Restore for Android:
- After adding a third-party OTP account, Duo Mobile prompts the end-user to enable Instant Restore and Third Party Restore.
- When restoring Duo Mobile accounts on a new device or after factory reset, Duo Mobile prompts the end-user to indicate when a Duo Restore account backup is available in the user’s Google Drive.
- Banners remind end-users to enable Instant Restore and Third Party Restore:
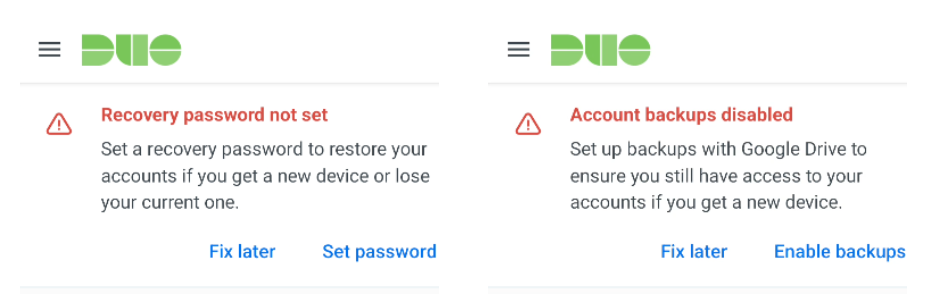
Duo Mobile for iOS version 4.28.0 released
- Miscellaneous bug fixes and behind-the-scenes improvements.
- Fixed Unexpected errors returned by the Duo Admin API in response to three API call scenarios:
- Synchronize User from Directory: Running a sync when the username has been updated in Active Directory, OpenLDAP, or Azure Active Directory and no longer matches the Duo username.
- Modify Administrative Unit: Changing the administrative unit name to a name already in use by another administrative unit.
- Add Integration to Administrative Unit: When the integration already belongs to an administrative unit.
- Fixed two bugs in Duo Passwordless:
- Chrome is out of date message displayed incorrectly when Chrome is up to date according to the application browser devices policy.
- Duo Device Health reporting now shows Passwordless authentications in the Duo Authentication Log.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: