- Cisco Community
- Technology and Support
- Security
- Duo Security
- Duo Release Notes
- D252: Duo Release Notes for Oct 28, 2022
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 10-28-2022 07:54 AM
Hello everyone! Here are the release notes for the most recent updates we’ve made to Duo.
Public release notes are published on the Customer Community every other Friday, the day after the D-release is completely rolled out. You can subscribe to notifications for new release notes by following the process described here. If you have any questions about these changes, please comment below.
What’s in this release?
New features, enhancements, and other improvements
- Duo Admin Directory Sync Now in General Availability
- UX Updates to Explain Phone Callback Authentications Blocked by Duo for Suspected Telephony Misuse
- Update to Duo Risk-Based Factor Selection Logs to Show Trust Assessment Results for Unsupported Applications
- Duo no longer binds the client’s IP address to authenticated sessions in the Duo Admin Panel or Duo Prompt
- CSV User Import Now Includes a Field to Import Hardware Tokens
- Duo Admin Panel Now Exports a Log of Duo Mobile App Instant Restore User Activity
- Duo Admin Panel Administrator Action Log Update
New and updated applications
- Duo Epic for Hyperdrive Version 1.0.0 Now in General Availability
- Duo Unix Version 2.0.0 Released
- Duo Device Health Application Stable Release for macOS and Windows 3.2.0
- Duo Mobile 4.27.0 for Android
- Duo Mobile 4.27.0 for iOS
Bug fixes
New features, enhancements, and other improvements
Duo Admin Directory Sync now in General Availability
- Extending the existing Duo Directory Synchronization feature, Admin Directory Sync lets administrators with the Owner role synchronize admin information into Duo from their Azure Active Directory, on-premises Active Directory, or OpenLDAP directory.
- Available to all MFA, Access, and Beyond edition customers.
- Customers already using directory synchronization will be able to re-use existing connections to expedite setup of Admin Directory Sync.
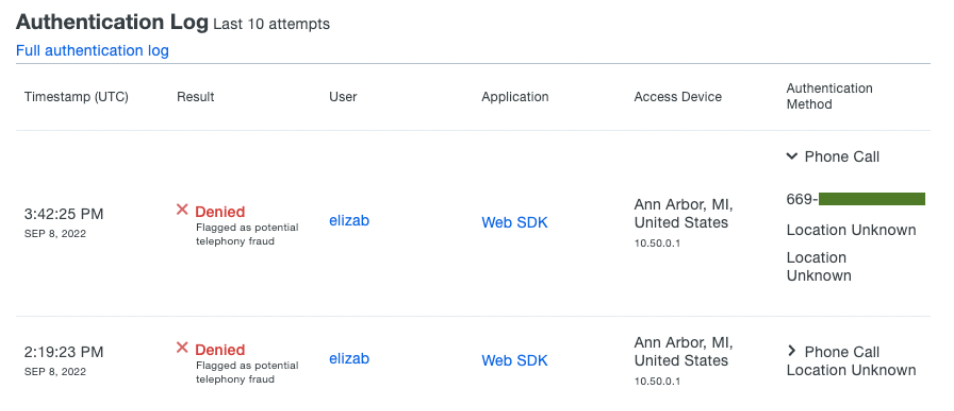
UX updates to explain phone callback authentications blocked by Duo for suspected telephony misuse
- End-users who request Call Me phone callback will see a Duo Prompt error.
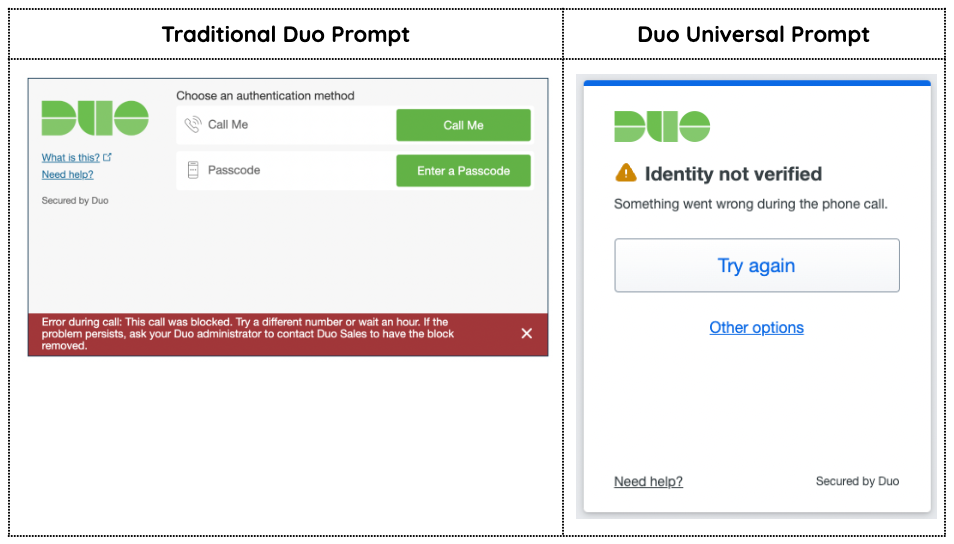
- The Authentication Log will show administrators when authentication is blocked due to potential telephony fraud.
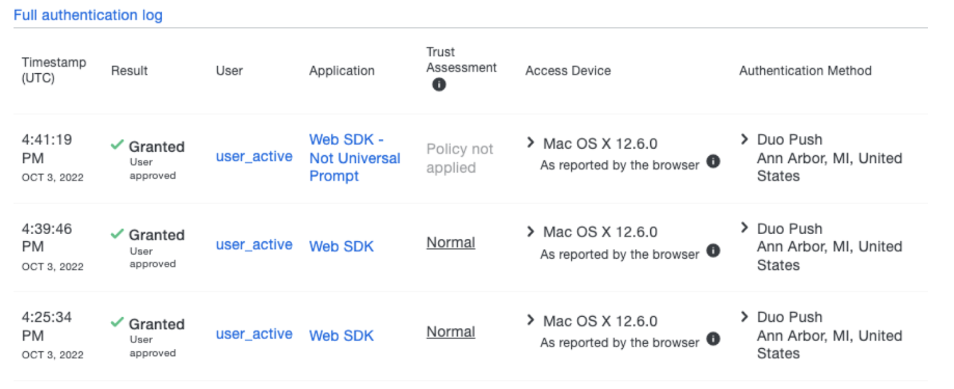
Update to Duo Risk-Based Factor Selection logs to show Trust Assessment results for unsupported applications
- If Risk-Based Factor Selection is applied to an application it does not support (i.e. any application that does not support the Duo Universal Prompt and is not a Duo Auth API application type), then Trust Assessment of authentications to that application will show in the Duo Authentication Log as Policy not applied.
Duo no longer binds the client’s IP address to authenticated sessions in the Duo Admin Panel or Duo Prompt
- By removing client IP session binding, users will experience fewer interruptions due to
Session timed outandLogin expirederrors when connecting over internet connections with frequently changing IP addresses. - This improves the experience for users or administrators interacting with Duo from internet connections that frequently change their outbound IP addresses and prevents the issues described in this knowledge base article.
CSV user import now includes fields to assign hardware tokens
- Populate the CSV user import field
token[1…N]with token serial numbers andtype[1…N]with hardware token type codes to attach one or more existing OTP-generating hardware tokens to new or existing users.
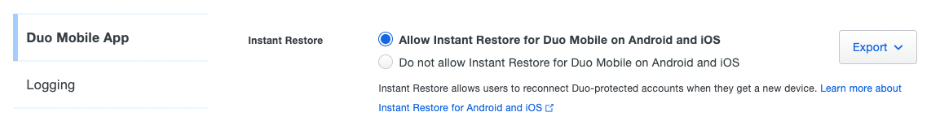
Duo Admin Panel now exports a log of Duo Mobile App Instant Restore user activity
- Customers who allow Instant Restore can export the new log from Admin Panel → Settings → Duo Mobile App → Instant Restore
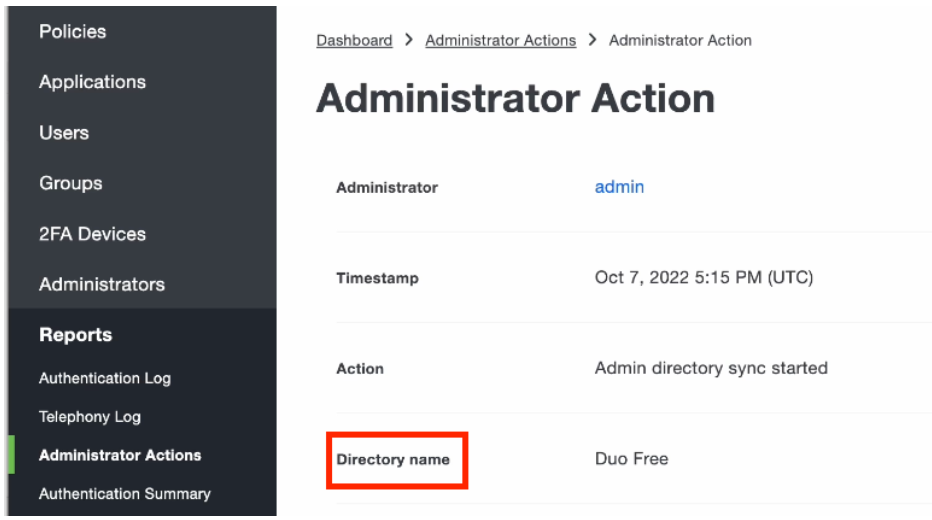
Update to the Duo Administrator Action log
- Directory name replaces the Object heading in Directory Sync actions.
New and updated applications
Duo Epic for Hyperdrive version 1.0.0 now in General Availability
- Read more in the Duo Blog: Cisco Secure Access by Duo MFA Secures Epic Hyperdrive Against Cyber Threats
Duo Unix version 2.0.0 released
- Updated
subehavior so that when UserA attemptssuto UserB then UserB will receive the Duo 2FA request. In previous releases, UserA would have received the 2FA request. This behavior is not configurable. See the Duo Unix FAQ for details.
Duo Device Health application stable version 3.2.0 released
-
- Updated remediation flows for macOS 13.
-
- Fixed an issue that could prevent the app from communicating with the prompt on some Windows 11 machines.
- Fixed an issue where Chromium based browsers did not trust our localhost HTTPs certificate.
- Fixed detection of Bitdefender.
Duo Mobile for Android version 4.28.0.1 released
- Added Amplitude as an analytics solution to drive effective product development. Amplitude will install with Duo Mobile enabled by default. Administrators may disable analytics tracking in the Admin Panel → Settings → Duo Mobile App → Usage Analytics.
Duo Mobile for iOS version 4.27.0 released
- Miscellaneous bug fixes and behind-the-scenes improvements.
- Fixed a security issue affecting Duo Push and Verified Duo Push authentication methods in Remembered Devices policies. The issue would allow a user with a Remember me session established with a Duo Push authentication method to access an application requiring the Verified Duo Push authentication method. The fix will invalidate Remember me sessions that were established using the Duo Push factor when the end-user logs into an application that requires Verified Duo Push.
- Country code trust assessment by Risk-Based Authentication has been fixed to step up the authentication factor properly, rather than return repeated errors, when an authentication device and an access device have mismatched country codes (for example, when a user is authenticating over VPN from another country).
- Duo Single Sign-On for Cisco Firepower with AnyConnect has been fixed to correct errors during certificate upload to the Firepower console has been fixed. Administrators may recreate the Cisco Firepower application in the Duo Admin Panel to correct certificate upload errors that occur.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Just added a correction, thanks @DuoKristina for the nice catch!
CSV user import now includes fields to assign hardware tokens
- Populate the CSV user import field
token[1…N]with token serial numbers andtype[1…N]with hardware token type codes to attach one or more existing OTP-generating hardware tokens to new or existing users.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: