Hello everyone! Here are the release notes for the most recent updates we’ve made to Duo.
You can subscribe to notifications for new release notes by following the process described here. If you have any questions about these changes, please comment below.
What’s in this release?
New features, enhancements, and other improvements
New and updated applications
Bug fixes
See all bug fixes
New features, enhancements, and other improvements
Skipping enrollment in Duo Passwordless now lasts seven days
- Clicking “Skip for Now” during enrollment creates a cookie in that browser that prevents the enrollment prompt for 7 days. Prior behavior would prompt the user at every authentication.
Duo Authentication Log now includes a unique identifier for authentication factors
- Where available, the Authentication Log now includes a unique identifier for the authentication factor that was used. For phones and hardware tokens, this identifier will also link to the details page in the Duo Admin Panel for that device.
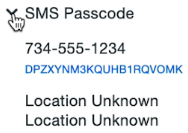
- Additionally, the endpoint response for the Duo Authentication Log when retrieved via the Duo Admin API now includes an optional key value within the auth_device field.
Operating system policy versions updated for Android
- Android 13 is now the current version for OS policy purposes and Android 12 has a status of supported.
Duo Admin Panel now allows disabling user bypass status option for user managers
- In Global Settings, disable the Allow admins with User Manager role to put users in bypass status setting to prevent User Managers from applying “Bypass” status to users.
New and updated applications
Duo for macOS version 2.0.0 released with security fix and offline access with Duo MFA
- Introduces offline access with Duo MFA.
- Adds support for Mac systems featuring the Apple M1 chip.
- The minimum supported macOS version is now 10.15 Catalina.
- Resolved an issue where smart card 2FA bypass did not enforce the requirement that the smart card’s assigned user matches the authenticating user (CVE-2022-20662).
- Resolved an issue where a time sync error upon contacting Duo’s service did not respect the local fail mode configuration and always failed open.
- Improved client logging with log-level filtering.
- Miscellaneous user interface enhancements and fixes.
- This security update was shared in the Duo Community on August 26, 2022.
Duo Device Health application public beta version 2.28.2 for macOS and Windows
- For macOS:
- Minor improvements and enhancements.
- For Windows:
- Fixed an issue with support script that could occur if the user has never started Internet Explorer.
- Added collection of .NET Framework version.
- Minor improvements and enhancements.
Duo Device Health application public beta version 2.28.3 for macOS and Windows
- For macOS:
- Minor improvements and enhancements.
- For Windows:
- Fixed an issue that could show language inconsistencies on Preferences page.
Duo Authentication Proxy Version 5.7.3
- Fixed a bug where the Authentication Proxy incorrectly included a reply message in EAP packets.
Duo Mobile for Android version 4.23.0 released
Duo Mobile for iOS version 4.23.0 released
- Miscellaneous bug fixes and behind-the-scenes improvements.
Bug fixes
- Restored an operating system policy option for use with iOS devices in anticipation of the release of iOS 16 later this year. The policy option of “If not up-to-date” allows patched iOS 15 and iOS 16 devices to both be treated as “up to date.”
- The addition of this policy option also restores functionality related to a bug that we identified internally on August 19, 2022 in which an iOS operating system policy configured to block and/or warn when the OS version is not up to date was reset in some cases to the default option that allowed all iOS versions to authenticate.
-
Duo notified customers affected by this bug on August 20 with a recommendation to review your policy settings and reconfigure them if needed.